Book Review: We Are Bellingcat
I was intrigued and impressed with Bellingcat's work before I read Eliot Higgins’ book, 'We Are Bellingcat'.

I was intrigued and generally impressed with Bellingcat’s investigative work prior to reading Eliot Higgins’ new book, We Are Bellingcat. Higgins is the book’s author and the founder of the collective of open source intelligence gathering investigators. I also have an affinity toward productive troublemakers, including those who “speak truth to power,” which is one of Bellingcat’s stated aims.
[According to UrbanDictionary.com“Speak truth to power” is a phrase often adopted by dissidents who've chosen a non-violent approach by using truth to oppose perceived acts of oppression by the government. The exact phrase is attributed to a Quaker pamphlet called "Speak Truth to Power: a Quaker Search for an Alternative to Violence," published in 1955; however, similar phrases with practicality the same meaning are found as far back as the 18thcentury.]
As Higgins discusses the wide range of tactics, techniques, and procedures researchers from around the world have used on different investigations, We are Bellingcat reads like a detective novel. The good guys in this book are working at their keyboards instead of, say, on stakeout in a car or pounding the sidewalk interviewing witnesses. Bellingcat is a collective of internet researchers who have built a reputation for conducting extensive, in-depth investigations into situations ranging from government misdeeds ranging from Russia’s downing of Malaysia Airlines Flight #17 in 2014 killing all 283 passengers and 15 crew members to Russia’s poisoning of a double-agent and his niece on UK-soil to the 2017 killing of 20 bound and hooded prisoners by a Libyan National Army death squad.
In its simplest form, open source intelligence gathering can be as straightforward as reviewing an individual’s Facebook posts to gain insight into their interests, communities and activities. At the other end of the spectrum, open source intelligence, also known as OSINT, can be used by law enforcement, human rights advocates, journalists, researchers, and ordinary people to uncover and document evidence of crimes, accidents, and any number of other incidents locally or across the globe.
Shining a light on the misdeeds or criminal activity of individuals, groups, non-state actors, or entire governments brings with it inherent risks, ranging from harassment to physical assault to murder. The Bellingcat investigators and countless other activists are at continual risk of personal harm. Female participants are particularly targeted by what Higgins calls the Counterfactual Community, comprised of conspiracy theorists, state propagandists, alternative-media outlets plus their supporters who keep disinformation alive and kicking.
The contribution of the non-technical public is increasingly important in open source intelligence gathering, as most recently evidenced by ordinary people submitting tips to the FBI to identify many of the pro-Trump rioters who attacked the U.S. Capitol building on January 6, 2021. Higgins writes that in 2017, Europol - the agency that coordinates criminal intelligence among European police forces - launched their Trace an Object initiative, asking the public to help identify clues related to child sexual abuse investigations. Europol has 40 million captured images of child sexual abuse that can offer clues to where crimes took place and who was responsible. For Trace an Object, Europol authorities crop out the victim from an image and show only the background, in the hopes someone might recognize something to help identify the location.
“A question often put to me is whether Bellingcat could be overshadowed by groups that replicate our methods, particularly big-budget news organization,” Higgins writes. “We are not worried; Bellingcat never sought to compete with huge media companies. From the outset, we have had two goals: find evidence and spread this field. We have gone a distance in both respects. And we still enjoy advantages, serving as a connective hub among experts and observers and rights activists and university scholars and citizens, all ready to launch themselves into investigations.”
What makes OSINT investigations different from some more traditional investigative journalism is that journalists may have to rely on anonymous or protected sources, which requires an element of the journalist saying “trust me and trust what I report,” and the public relies, in part, on the reputation of the journalist. Open source investigation depends not on confidential sources but instead on transparency. Effective OSINT investigations provide a retraceable roadmap that others can follow to arrive at the same conclusions. As these types of investigations are increasingly contributing to legal cases, their submission as evidence often requires proper documentation and archiving of procedures. Bellingcat’s efforts over the years have contributed to the development of such evidentiary standards of care.
“Today, Bellingcat finds itself in an unusual position. We are not exactly journalists, nor human-rights activists, nor criminal investigators, but at the nexus of all those disciplines,” Higgins writes. “The Bellingcat method has expanded far beyond the foundational principles of ‘Identify, Verify, Amplify,’ encompassing an ethic, a social mission and a drive for accountability. We will remain at the vanguard of open-source investigation. We will break major stories. We will present evidence and insist on the primacy of fact. We will act as a firewall against disinformation. And we will encourage as many people to join us as possible.”
I had the opportunity to participate in a three-day Bellingcat OSINT online workshop led by three of its members, where a number of the research situations discussed in the book were broken down into the key steps taken and obscure clues followed to arrive at their conclusions. While We are Bellingcat is not intended to be a “how to” guide, it’s too bad that many of the eye-opening images and photos shared in the workshop I attended weren’t able to be included in the book, presumably due to privacy and copyright issues. The stories Higgins shares are even more fascinating than he’s able to relay in words alone; nevertheless, his narrative draws the reader into Bellingcat’s highly competent and impactful world of online investigation.
Bottom line: this book was a fast, fun read where I said “Wow” out loud repeatedly as I read it.
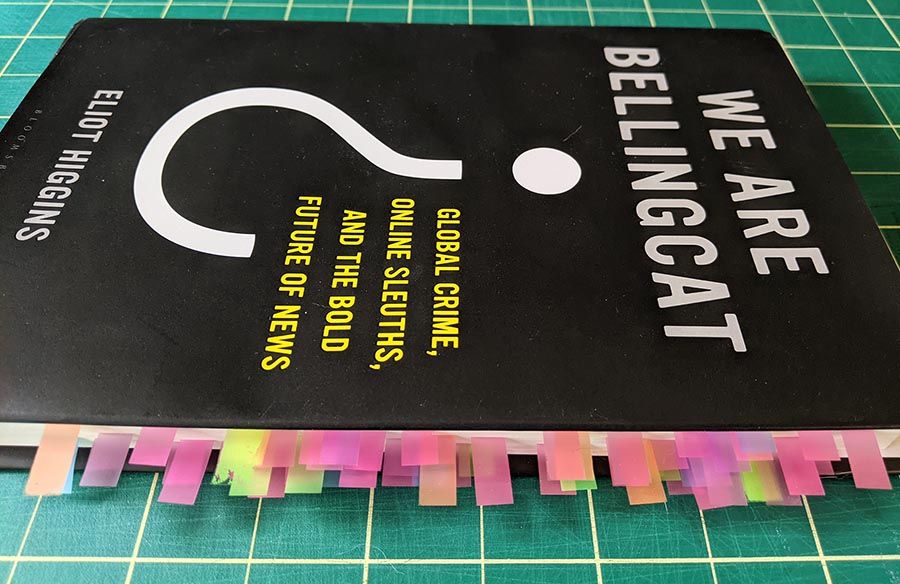
Higgins shares an abundant list of resources, websites, and organizations that play a part in Bellingcat’s world (and in the OSINT community in general). When I read non-fiction and reference books, I tag important details with colored plastic adhesive tabs (such as 3M Post-It flags), with different tab colors corresponding to different categories. For We Are Bellingcat, my categories included: Tactics, Tools, Reference Sources, Zen of OSINT (Higgins is oftentimes philosophical on what Bellingcat does), and Words to Remember (Higgins also has a good vocabulary). I also write in my reference books (gasp!) to mark the really good stuff. My copy of We Are Bellingcat is now rife with both tabs and ink.
At a minimum, this book is a fascinating primer for readers both beginning or experienced in journalism, research, human rights investigation, and other disciplines where open source intelligence gathering can be applied as an oftentimes powerful tool to uncovering the truth.
Daniel Farber Huang is author of “NOWHERE TO HIDE: Open Source Intelligence Gathering” about how the FBI, Media, and public identified the January 6, 2021 U.S. Capitol rioters and also author of “Practical Cyber Security for Extremely Busy People.” He is a strategic consultant helping a wide range of companies in different industries reduce risks at all levels of their organizations, including their cyber security.

