Chinese Threat Intelligence: Part 1
A modern primer on threat intelligence in China and a non-specific inventory of the threats we're facing from China. Part one of a three part series.
Welcome to my primer on threat intelligence in China, this is going to be a non-specific inventory of the different general threats we’re facing from China. China’s threat landscape differs from the typical Western threat landscape in a couple of different ways.
This is essentially going to be a running document. This is important, as the primer should be viewed as a current report, valid only until the next big change in the threat landscape. If international legislation dictates a legal change in international behavior in cyberspace, this will drastically change the threat landscape. If a conventional confrontation takes place involving China, the landscape will also change. Every day brings the potential of a new threat appearing and old threats changing behavior, but very rarely do old threats disappear. They merely change shape.
A General Primer
This section will break threats into general categories which will then be refined into a Sino-centric definition. This list will not be all-inclusive, potentially glossing over some threat actors, but will be general enough to describe the big ones. I’ll also briefly describe some examples of each type.
Generally, threat actors are described by their motive. Hacktivists, as discussed below, are politically motivated, and are described by their political motives. Hong Kong hackers are pro-democracy for Hong Kong, while mainland hackers are for the inclusion of Hong Kong into the governing structure of the mainland. This means that while I will name subgroups of hackers, these are further divisible into more subgroups. Anonymous, for example, is divided into ‘sec’ subgroups with different political aspirations. APT’s within governments have completely different targets and TTP’s.
Hacktivists
The aforementioned hacktivist groups are the modern twist of activism. They break sites to deface their front pages with political messaging, steal PII (Personally Identifiable Information) to ‘dox’ their targets, posting the PII in the public to threaten or coerce or damage the reputation of their targets. They also have been known to use social media as a disinformation realm to change public opinion about a political subject. Hacktivists often have an online and a ‘real world’ movement.
The usual Western example of hacktivism is Anonymous. Anonymous is a collective founded in the early 2000s, roughly organized into a sort of guerilla like collective organized around a central sort of anarchist ideal system. They have taken up multiple causes, from animal abuse to privacy, from globalism to nationalism. Anonymous saw its prime years ago, as I posted a blog on my old medium, linked here, about the inevitable fall of Anonymous.
A Sino-Centric example of hacktivism is the nationalist hacker collective HUC. The Honker’s Union of China, mentioned in my previous blogging series, was also a reactionary element similar to Anonymous. They were largely decentralized, operating out of private chat channels and hidden blogs, and used tools circulated within the pseudo-closed group. Membership was roughly defined as an agreement to the general anti-Western sentiment. Since it was a largely reactionary and decentralized movement, it generally disappeared when political tensions calmed down.
Hacktivists should be viewed on a case-by-case basis. Anonymous is a broken and dead movement, generally supported by unskilled actors or opportunists that take advantage of generally easy to exploit, known vulnerabilities. It was a rare day when a member of Anonymous utilized a complex 0-day or took part in an operation that took skill and patience, but there were certain ‘secs’ that had members that had a pretty considerable amount of skill. HUC was the same, launching DDoS attacks, also heavily utilized by Anonymous, against an infrastructure that was very vulnerable to those attacks. HUC also had members, such as Li0n, that displayed a higher level of skill, similar to members in Anonymous that achieved relatively complex attacks.
That isn’t to say that threat from these groups are low. They are volatile, organizing very quickly with a heavy influence on social media in reaction to political climate. They are difficult to fight and find, because of the general decentralization of the groups. While hacktivist groups utilized known vulnerabilities, these vulnerabilities are often widespread and often unpatched. Hacktivists are a threat because of how large these collectives tend to be, and can attack from many angles at once.
Advanced Persistent Threats
This is the meat and potatoes of what the current MSM likes to talk about. It’s infuriating that this is the only threat that currently gets attention, but it does deserve a large amount of attention. Currently, as nation-states start to develop their own national cyber espionage and operations divisions, APTs have grown in popularity. Largely because of private security companies like Mandiant, FireEye, and Kaspersky, these APTs have garnered more and more attention.
APTs aren’t necessarily nation-state backed. There have been APTs that have never had provable nation state backing. APT status merely implies advanced Tools, Techniques, and Procedures (TTPS) and an insistence on persistence, instead of smash-and-grab one-off attacks. That being said, the more well-known threat actors have pretty hard evidence of nation-state backing.
A Western example usually surrounds the US National Security Agency, known in security circles as EQGRP or Equation Group. This threat actor is incredibly advanced, using stealth techniques that are either entirely new and never seen before, or are learned from previous operations within enemy networks. They ensure an incredible level of stealth, using hard to trace protocols bounced around air-gapped networks in order to evade active defense measures. They often aren’t found until they have already left the network.
Targets of EQGRP tools often coincide with known targets of US espionage, including targets in the Middle East, China, and Western European nations. This is a common way to attribute a threat group to a nation-state actor, sort of following the “if it looks like a duck and quacks like a duck” philosophy.
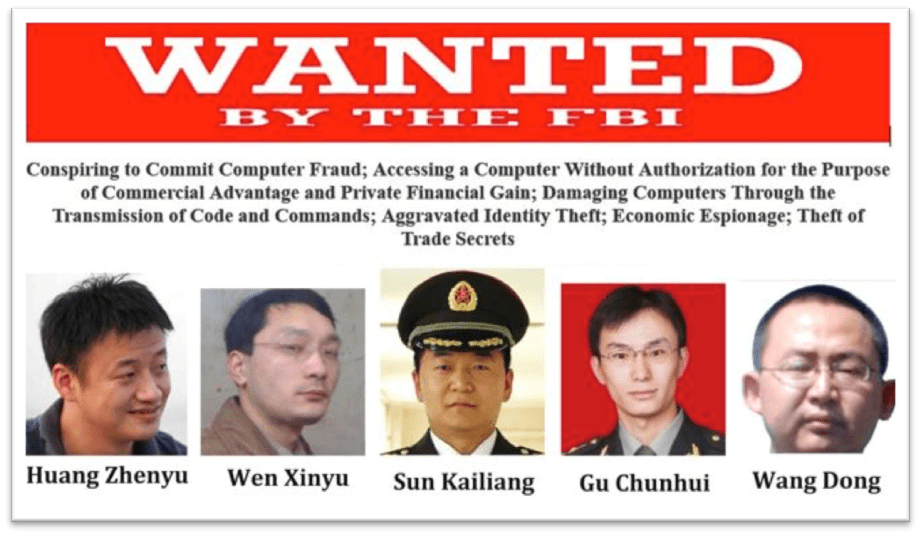
The Chinese ally to Equation Group can be considered APT1, first reported by Mandiant. The groundbreaking report was one of the first widespread reports of international cyber espionage, and detailed an incredibly stealthy and persistent group, known to stay in target networks for years at a time. This group targeted multiple, diverse industries including healthcare and defense, and was very successful at infiltrating all parts of target networks and siphoning off data without being discovered. This report also lead to the first international indictment of nation-state hackers, five Chinese hackers allegedly involved with the PLA’s targeting of the US.
APTs should be thought of as an advanced threat, meaning that if your network isn’t worth attracting an advanced actor, it shouldn’t be included in your threat landscape. While you may think your beer inventory app is pretty neat, and you sold it to a couple of local bars in your hometown, I wouldn’t worry about Russia hacking your Firebase database and stealing customer data. You should be worrying about criminal groups looking for low hanging fruit, not a targeted and persistent attack by President Xi himself. That being said, if you do handle data that could feasibly be an intelligence target, it is very difficult to secure that data from this kind of threat. If you’re handling critical systems like that, you better have an IT security team and budget to match.
Criminal Groups

Criminal groups, just like the mafia of the past and gangs of the present, vary by location, intelligence, and motivation. These criminals tend to focus on financial gain, selling card dumps, doxes, and malware including exploit kits, worms, access to botnets, and spam services. Criminal groups make alliances and hold fierce grudges with other groups, warring over territory and even placing hits on other groups.
Generally speaking, criminal groups can be organized traditionally by known membership or by membership of the forum that organizes them. For example, while I can name different sub-groups on Hack Forums, a common script kiddie forum, generally they’re referred to as Hack Forums “threat actors”. Honker’s Union of China had subgroups, but were generally named by the forum they organize on. Sometimes, the designation is important, like when Lulz Sec was around and the distinction between them and the general Anonymous movement was important.
There are literally thousands of criminal groups worldwide. This includes carders, malware authors and distributors, botnet operators, and bulletproof hosting vendors. They also tend to be closed off to the public, using forums and services that are invite only. A Western example would be Hell, a forum from the past that was thought to house some serious Western actors. This was considered the ‘serious’ version of Hack Forums, housing the annoying, inexperienced actors and scam artists looking to make a quick buck off of inexperience skids.
A Chinese example would include HUC or the various small forums. Generally speaking, because of the crackdown by the government and heavy dependence on surveillance, the Chinese criminal hacking realm is a little more underground than communities in the West. They’re difficult to find, closed off, and generally not indexed by search engines. China has also taken a page out of Russia’s books, enlisting criminal hackers to work for the government, likely instead of jail time.
Criminal groups should be viewed as a primary threat for just about anyone. There are a lot of them, and they aim for low hanging fruit as well as tough to crack systems. They vary in intelligence and often use public tools to hide their identity. They aim for financial gain, meaning they target PII and other confidential information.
Criminal groups can and often do enlist target networks for use in future attacks, meaning some focus more on persistence than others in order to ensure business continuity. Criminal groups are a huge threat, and can cost different industries millions or more in damages. This should be viewed as the biggest threat to most networks because of their high prevalence to impact ratio. Criminal groups are here to stay as well, grossing millions of dollars in revenue last year.
Automated Attackers

This is a newer addition, and one that doesn’t yet have a prevalent Chinese example. Automated attackers include worms with exploits that scan the local subnets and the internet as a whole for low hanging fruit in the form of vulnerable systems. This widespread worm spreads like wildfire, and can create botnets that can be used for password cracking or massive DDoS attacks.
An obvious example would be the Mirai botnet, which spread automatically to IoT devices using a list of default passwords. These IoT devices were used in massive, record-breaking DDoS attacks against the very backbone of the internet. These attacks dwarfed all others in scale and power, but utilized a relatively simple method to spread.
In terms of threat, I assess this kind of attack to grow in popularity and impact. After Mirai, threat actors began to pay attention, resulting in clones like Reaper which had a very similar level of impact. They are going to target the inherently vulnerable nature of internet connected devices like IoT and cloud services. They can have a massive impact, but they carry a pretty predictable attack cycle. This means sysadmins can catch on quickly and develop defense procedures that can detect and block automated attacks. This leads to an endless cat and mouse game between autonomous malware devs and blue team operators.
In Conclusion
China carries many similarities to the West in terms of their cyber threat landscape, but have a few notable differences in terms of specifics. The nation-state backed groups from China carry a particular threat, inherent in their nationalistic pride and size of their military cyber divisions. They also have far reach in their private industries and underground, leading to the possibility of hybrid threats that are nation state backed but take the form of private or criminal actors. In general, though, Chinese actors should be approached with caution. Their TTPs are evolving and they are learning from previous engagements. The next few years will see a growth of Chinese threat actors, and the industry should evolve to reflect that.
Part two is coming next week and will focus on the high points!