ChromeCast Leaks App Data
One night I checked my local network for PS4 traffic, instead something else caught my attention. I saw something strange and this is the story of my ChromeCast bug.
One night I was waiting for a friend to do some collaborative bug bounty hunting and I was bored, so I thought of checking my local network to see if someway I could see anything remotely from a PS4 that I recently bought in order to exploit. But instead of my PS4 I saw something else that caught my attention, this time I saw something really really strange and this is the story of my ChromeCast bug.
It all began with a normal network scan to see the details of all the hosts within my network. I normally use nmap but this time I was using a new tool that I had only discovered recently which I found while I was searching for a way to use the network printer (Trust me this kali linux of mine has given me lots of problems and I learnt a lot while fixing them). The tool was Avahi Daemon. Within this daemon, there's a feature called Avahi-Discover. According to the Linux Man page for avahi-discover, it shows a real-time graphical browse list for mDNS/DNS-SD network services running on the local LAN using the Avahi daemon.
So I thought of giving this tool a go because I was not able to find the exact IP for my PS4 Console and this is where I saw Chrome Cast's Device name too.
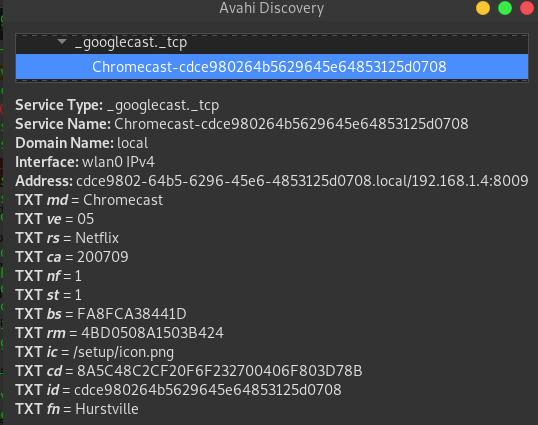
I don't know why, but my instinct led me to click on it before my PS4's IP and there was option to see a full detail of the device. After clicking on the full details view, I was amazed to see that whatever application was being streamed via Chrome Cast showed the name of the application, Netflix in my case (at this point of time, I only saw the application name). I was trying to see if I could be able to see anything else but failed in almost everything. If you have any idea, what shall I try or if you wanna try it out, it's still there. For this to be a success, you need to be connected to the same WiFi network (does not matter even if its your Neighbor's wifi :p ).
Install Avahi by using the following terminal command:
apt-get install avahi-daemon
Have fun!