Credential Stuffing Attacks Are Rising In Popularity, But They're Easy to Stop
Why have rudimentary attacks such as credential stuffing become so common? Because hackers prefer to spend their time using more efficient and less costly attack methods.
Hackers are becoming cleverer every day; it’s what makes effective cyber security so challenging. Constantly, new vulnerabilities and exploits are being found, each one more sophisticated than the last. Why then have rudimentary attacks such as spear phishing and credential stuffing become so effective and common?
Because hackers prefer to spend their time using more efficient and less costly attack methods; hence the recent swell of success with credential stuffing attacks.
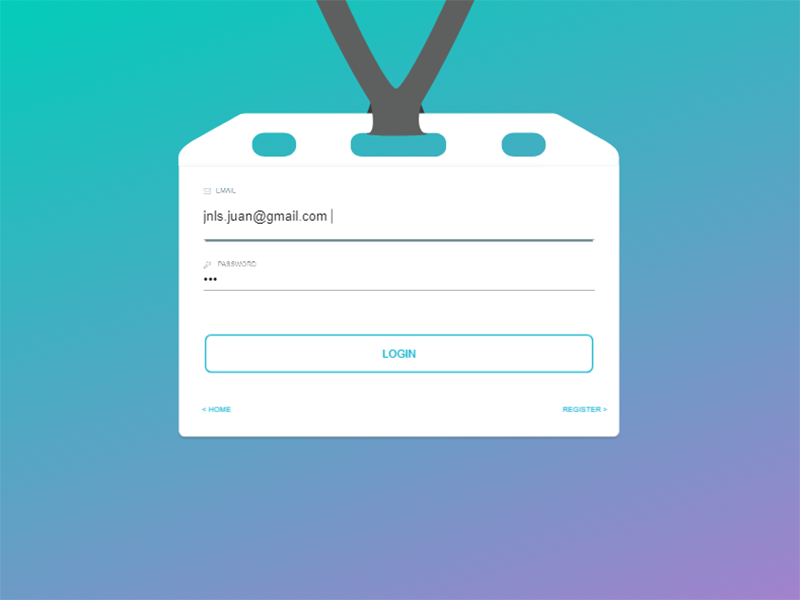
A credential stuffing attack consists of an attacker taking already stolen credentials and "stuffing" them into a login portal to find common usernames and passwords, despite the un-creative name, these attacks are growing in popularity and have become very effective. To name a few recent successful credential stuffing attacks: Dunkin Donuts, Nest, and Dailymotion. These attacks were successful because a lot of people use the same credentials with multiple digital services. It only takes one breached database to gain access to multiple accounts across the web.
Credential stuffing is not a new phenomenon, in fact, it’s been around for 6 or 7 years. However, its popularity is surging as data breaches become larger. In the US, the average size of a data breach is over thirty thousand records and growing every year. Considering majority of people don’t update their passwords as frequently as they should, even older databases can be a treasure trove of credentials to use in future attacks. While hackers tend to only have success with their stolen credentials around 2% of the time, 2% of 30 thousand is still enough to motivate most solo hackers.
They have engineered methods to automate the credential checking process, so it requires little hands-on work. Once hackers gain access to accounts, they normally do one of three things: sell access to the accounts on the Dark Web, sell the personal information inside the account, or use the personal information themselves to target the users for other attacks.
Thankfully, credential stuffing attacks are one of the simplest forms of attack to protect yourself from. Just a few easy steps are required to make yourself almost invincible to these types of attacks:
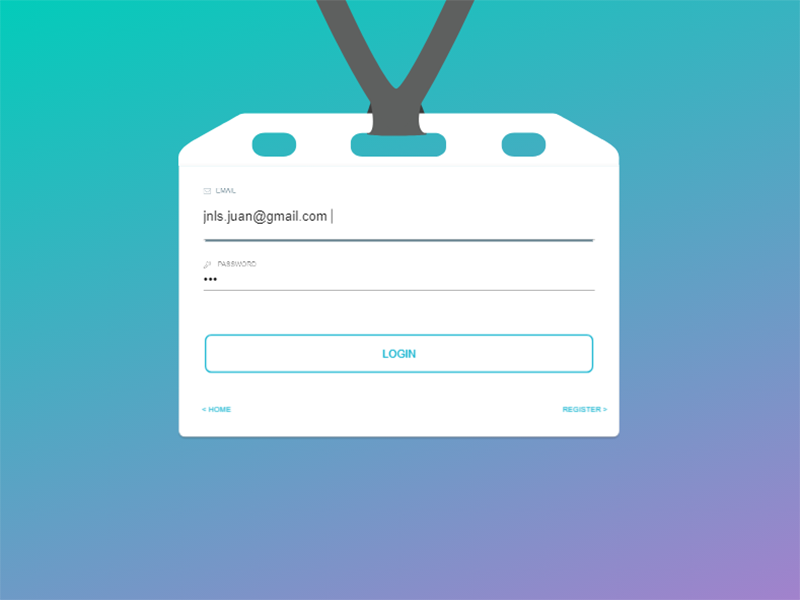
Use different usernames and passwords for every site:If you have a different username and/or password for every digital service you use, then a breach at site A becomes only a minor annoyance. When you reuse credentials, a breach at one site becomes time-consuming because it involves changing login information at multiple services. Plus, credential reuse puts you at a greater risk if you aren’t staying up-to-date on data breaches, or if a company waits too long to disclose a breach.
Your credentials could be available on the open web for months without you knowing. This might be viewed as an inconvenience because you now must remember every different password and username for every service you use, however, it isn't an issue if you follow my next recommendation
Use a password manager: Password managers are amazing, plain and simple. They are remarkably easy to use and setup. They are a simple and low-cost precaution, and they’ll greatly increase your protection against a variety of attacks. I recommend LastPass. It has a free option, and a plugin for Chromium-based (Chrome, Brave, Opera) and Firefox browsers. Whenever you create a new account, LastPass will ask if you want to store your credentials in their vault. If you say yes, the username and password pages will be pre-filled when you revisit that site.
Super simple right? Just make sure you choose a truly unique but memorable password for LastPass since it contains all your passwords! Lastly, LastPass has a super cool Security Challenge feature which checks your passwords for weaknesses, reuse, or whether they have been compromised.
Update your passwords regularly: Common security protocol is to change your password every 90 days at least. However, I think every 90 days is overkill if you follow my first recommendation. Strong and unique passwords are their own defense against credential stuffing attacks. Still, it is a good idea to conduct regular audits, two or three times a year, on your passwords.
Look to see if they have been included in any data breach. A great service for this is haveibeenpwned.com.It works by entering a username, email address, and/or password and the website then compares your input to available credentials on the web. It will notify you if any of your credentials have been included in a breach.
Use two-factor authentication wherever you can: 2FA, for those not familiar with it, is an authentication tool which requires users attempting to log in to a service to provide two different forms of "evidence" proving their identity. For example, someone wants to log in to Facebook, so they enter their password. Facebook then sends them a text with a secret code to their phone. They then give Facebook the secret code and are granted access. 2FA can stop almost all credential stuffing attacks because hackers most likely won’t have access to your second form of authentication. Most digital services offer it as a feature nowadays.
If they do, turn it on. It only requires a few more seconds to log in. You'll be thankful you did when your neighbor's frequent flier account gets hacked and thieves steal his miles. If you utilize a service which does not offer 2FA, hound them until they do or strongly consider not using them. Everyone should be offering 2FA by now, so I would be wary of a services' other security policies if they aren't offering it.
Credential stuffing attacks are some of the easiest to protect yourself from. Unfortunately, many people follow poor cyber-hygiene leaving them vulnerable to very rudimentary attacks like these. Follow the steps above, and you'll be protected from credential stuffing attacks and the like.