Notes On CVE-2019-0708 (RCE 0day)
This week a major RCE vulnerability has been spotted in the wild which affects affects a number of Microsoft OS's including Windows 7, Server 2008, Windows 2003 & Windows XP.

This week a major vulnerability has been spotted in the wild, RDS (Remote Desktop Services) or known as Terminal Services suffered a major encounter with a security flaw that allows anyone to execute arbitrary code through sending a specially crafted packet to a DHCP server running a vulnerable version of Windows.
The flaw also known as CVE-2019-0708 (Remote Command Execution) affects the following version of Windows including Windows 7, Windows Server 2008 R2, and Windows Server 2008, Windows 2003 & Windows XP, all of them being in-support and out-support versions of the OS.
It has been noted that the security flaw is "wormable", meaning an exploit can be used to infect other devices on far more networks as there is a high chance of a spread due to systems with default passwords & no passwords. The exploit can be ran with a script that scans for ranges within systems that have port 3389 open using a vulnerable version of windows.
Microsoft has released a patch for CVE-2019-0708 on the vulnerable version of windows including the out-support versions, but there is still a huge risk as over 4,000,000 systems run off RDP, 12,000 running on Windows 7 & over 2,000 running Windows XP so chances are that many vulnerable systems are still in the area of impact from this security flaw.
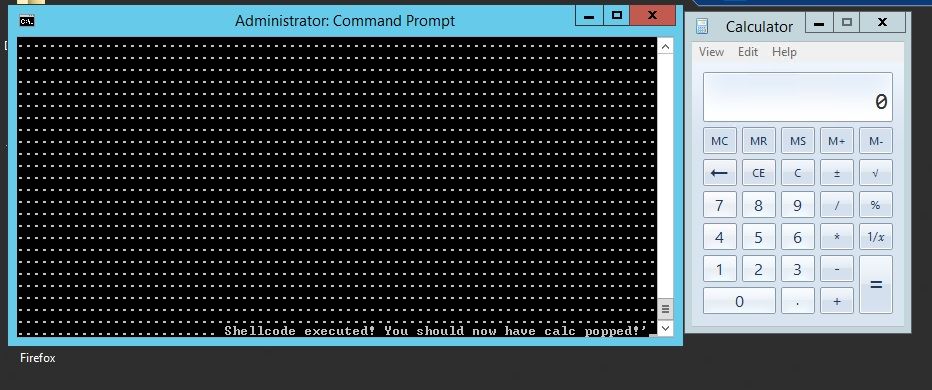
The PoC shown above executes shellcode through a request with the attached exploit, this is remote and not local which is why it has everyone wondering if an exploit is being used to takeover systems and run ransomware on them. A similar case has been noted in the April 2018 Ransomware attack on Cleveland Hopkins Airport where it was said that the KACE 8.0.318 systems were vulnerable to CVE-2018-11138, allowing anonymous users to execute arbitrary commands in the system.
This severe security flaw tells us that severe vulnerabilities can exist in the maturest of software systems, I just hope that whoever finds them is ethical about disclosing them. I hope you enjoyed this quick-write up on the newest RCE flaw, thank you for reading.
For more write-ups follow @mewsecurity on twitter.
~ Mew


