DEF CON Groups: What Works in 2018?
Thinking about starting your own DEF CON group? Join security researcher Lacey Kasten in an investigation into what works and what doesn't in 2018.

want that minty-fresh #defcon feeling all year long? Join a DC Group. Can't find one? Start one! http://t.co/UcwM2skXDc
— DEF CON (@defcon) August 18, 2014
The days of deadly solar radiation season (as the DEF CON official blog kindly refers to summer sun) are coming to an end and it’s time to cozy up within our local communities. Hacker summer camp (see: this helpful guide for the uninitiated) may be over, but the first DEF CON local group meetings directly after are worth going to even if you did not attend the con storm of Las Vegas this August.
Typically, new members show up the first meeting after DEF CON for a number of reasons:
a) They just learned that there’s a local group in their area.
b) They just remembered that there’s a local group in their area.
c) Because it’s socially more comfortable to be “the new member,” when you have the commonality of hacker summer camp memories to ignite conversation.
This year at DEF CON, we saw the targeted efforts of Women in Security and Privacy (WISP) to bring 57 sponsored attendees to DEF CON 26. Leading up to August, each sponsored attendee was given opportunities to network with a dedicated Slack and the Twitter hashtags #WISPDEFCONSQUAD and #WISPDEFCON. Because of this, women from multiple countries, experience levels, and many first-time travelers were able to attend a convention they had only ever dreamed of being able to visit.
The @wisporg #wispdefcon ladies are here! #wispdefconsquad rolling deep at @defcon! Thank you donors for making this possible and thank you @deanpierce for donating your space for this meet up! pic.twitter.com/VcxeyyLOfY
— WISP (@wisporg) August 11, 2018
Post-con the WISP DEF CON Slack came to a quiet as recipients returned to their lives back home, but there were quite a few women dedicated to staying connected. For many, this was their first and boldest inclusive welcome to a DEF CON related community and the incentives to carry on this year's momentum were vital.
One first-time DEF CON attending recipient from the 57 WISP sponsored attendees posted a tweet sparked by conversation that happened during DEF CON that picked up a myriad of interesting responses about official DEF CON local groups:
Making a Defcon group for my area because apparently we have nothing!!!
— g0neph¡sh¡ng (@_42LU) August 17, 2018
How did you start your group?
How did you get people to join or get the word out there?
I had some very encouraging advice while I was in Vegas but would love to hear from others as well!
One responder to g0neph!sh!ng (@_42LU)'s thread by the name of Jonny Xmas (@J0hnnyXm4s) mentioned a panel he was a part of at BSides Nashville, 2016, covering several frameworks to consider for local group structures.
A lot of what Johnny Xmas and Chris Carlis from BurbSec share during the panel at BSides Nashville, 2016, rings true in 2018 and can be applied to DEF CON groups. In fact, CitySec groups serve as great models for local DEF CON groups. Chris Carlis makes it a point to note that when you expect dues from members (e.g. ISACA meetings), people expect returns for what they've paid and the meeting becomes transactional. In regards to fostering community, exclusion based on finances is going to eliminate a large number of your potentially valuable and interesting local members. Most groups can also agree that sales-heavy pitching is both awkward and destructive to the flow of group meeting, as this also pushes meetings into a transactional realm.
Now here's where the hot debate begins: Are presentations valuable or detrimental to DEF CON groups?
Talks (or presentations) will always be a go-to for event programming of InfoSec groups at large. Sometimes presenters are difficult to approach immediately after presenting at big conventions like DEF CON or Blackhat. Given an opportunity to speak in their local groups, often with amended versions of their DEF CON or Blackhat talks including additional slides, is valuable for both presenter and listeners. Having presentations at local groups also allows DEF CON groups to pull out-of-town guests to speak and network with the close-knit audience.
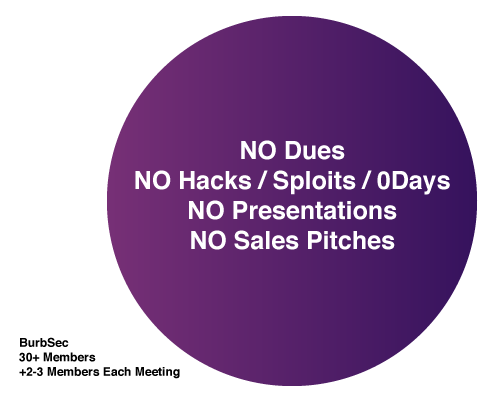
Both Johnny Xmas and panelist, Kate Vajda (@vajkat) cited reasons why presentations often cause issue for local groups. Johnny Xmas brought up the point that presentations break the flow of conversation, the natural ambience of a chill atmosphere where no one is being thrown in front of the spotlight and no one is being forced to sit through uninteresting talks. Kate Vajda, another panelist, spoke about her involvement with Misec, a group located in Southeastern Michigan. She mentioned that employing "lightning-talk" rounds where every member present is required to speak for 2-5 minutes, negatively puts pressure on newcomers, and can keep quiet members (or those with social anxiety) from joining.
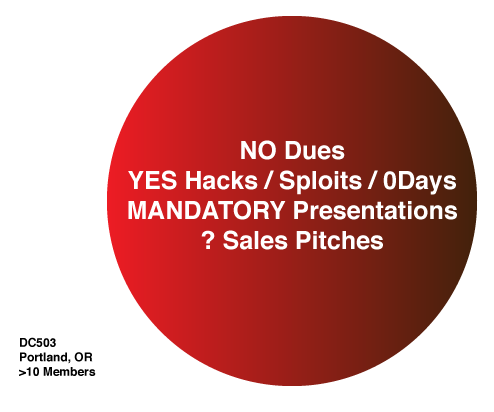
The current iteration of the DC503 group framework is modeled off of AHA! (Austin Hackers Anonymous)'s aggressive "turbo-talk" rules:
- You must participate to remain a member.
- There is no recording or filming allowed.
- What happens at AHA, stays at AHA.
- Keep your talk under 10 mins.
- Pitching product/company or recruiting for headcount? YOU MUST BUY BOOZE
The AHA! rules page goes into specifics about each item, adding additional features like, "If you go over [time], expect to be heckled and interrupted until you stop talking. If you must exceed 10 minutes, it better be damn worth it." AHA! goes as far as to threaten to remove attendees who show up and consistently do not participate with a presentation off the venue premises. It's important to recognize that AHA! is not a DEF CON group, nor a CitySec type group. AHA! believes in a radical way to break the ice, keep meetings active and informative, and offer a venue for presentation. While these rules might seem harsh in comparison to Misec, or your local framework, to the right people and right audience, this framework works fantastically in Austin.
Are there official frameworks suggested by DEF CON groups? And what, if any, governance happens from the parent organization?
DEF CON does not act as a governing body to enforce baseline code of conduct or frameworks on the localized DEF CON groups. The only formal aspect is naming and relates to area codes / international calling codes. For example, DC503 is based on the 503 area code of the Portland, OR metro area, and international groups must include the additional international calling code (as April C. Wright (@aprilwright) explains, Costa Rica would be 11506.)
@defcongroups Yes there are international rules - Naming is based on country dialing rules. So, to dial Costa Rica from the US, we would need to dial 11506 https://t.co/OtjD9NTvHs This is specified in the "How to start a DEFCON group" post on the site. Sorry.
— April C. Wright (@aprilwright) July 9, 2018
Otherwise, the official DEF CON groups FAQ keeps it vague and supports the imperative of inclusivity with a nod to 2600. Coincidentally, 2600 DOES define a framework for 2600 meetings and does not orphan local groups from the parent organization:
"DCGs are not intended to compete with any other computer groups, such as 2600, but rather to provide yet another gathering place for the discussion of technology and security topics. DCG meetings are open to anyone, regardless of their skill, age, job, gender, etc. DCGs are designed to help you learn new things, meet new people, mentor others in areas you may be strong in, and provide some cohesion within the hacker culture and it's members." – From the Official DEF CON Groups FAQ

The description of DC503 stands out among other official DEF CON groups listed in the registry:
"We are Portland's chapter of Infosec-fightclub: everyone must present something. Meetings are round-table style, closing with a headline speaker who presents in more depth. Show us what you're working on, why it is worth your time, and why we should care. All presentations are off-the-record, we want to see each-other's sketchiest shit."
In this way, DC503 actively promotes or encourages members to share sensitive information / techniques without the same umbrella of safe disclosure that the parent conventions can provide. This is how DC503 justifies its misappropriation of the AHA! "turbo-talk" framework, and obfuscation of location information for the meetings (which notably, AHA! doesn't even do.) The idea is if you show up to other local events and ask strangers, one might tell you how and where to find DC503 (spoiler: it's definitely not at the biggest makerspace / hackerspace in Portland.)
The 2600 guidelines address solutions for some of the pitfalls DEF CON groups can fall into, while taking an adjacent approach than the frameworks Johnny Xmas & other panelists shared:
a) 2600 meetings are held in public places, out in the open.
b) Locations are posted on the 2600 website, and meetings are held on the First Friday somewhere between 5 and 8 pm for ALL GROUPS.
c) 2600 has nothing to hide that is occurring during meetings (re: hacks, sploits, 0day required, and responsible disclosure)
d) 2600 meetings "don't do illegal things and we don't cause problems for the place we're meeting in"
e) 2600 requires check-ins from the organizer to the parent organization, or else their groups will be dropped from listing on the site
Some serious questions need to be asked about whether or not the current DC503 model works for Portland. Questions like, "If you have to force people to give talks to participate, does that suggest, maybe, that they don't want to give talks?" And more open-ended DEF CON groups community questions like, "If you're employing the AHA! framework to a DEF CON group, does this work to provide genuine space and inclusivity for local hacker communities? Is this in the spirit of DEF CON itself? Do you deserve to call your group a DEF CON group if it excludes members?"
What is an example of a framework that is successful? How do we measure success of a DEF CON group?
The InfoSec community is full of critical, cynical individuals who in the worst of times might even want to commiserate over a pint or work on completely unrelated maker projects. We also have to admit that we're an industry rife with "imposter syndrome," exacerbated by how we are expected to always be on our toes, ready to learn or adapt to new threats and intel. To loop back around to the Johnny Xmas, et al. BSides talk, you're going to neuter your group participation if the meet up you're going to after work is also work. Sitting through, and giving consistent presentation to be allowed to join is work.
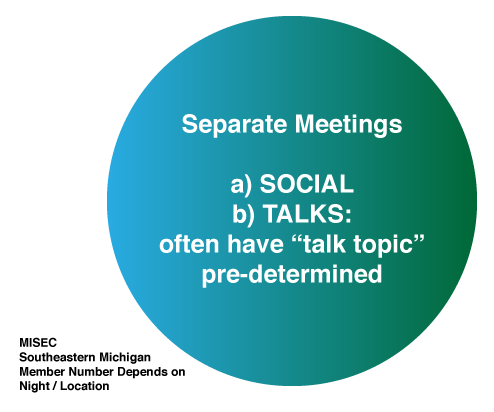
With this in mind, a structure similar to Misec, discussed by Johnny Xmas et al., has great potential to exist as a model framework for DEF CON groups, old or new.
The ideal space for talks will be a venue that has enough physical space and projector / AV technology for presentations. If the city has a makerspace or hackerspace, these are great venues that should be equipped for presentation. Control of people moving in and out of the space is valuable from a security perspective but also to avoid disrupting presenters and the audience. The room should also be ADA compliant and easily accessible, preferably from the ground floor. There's a lot of value in not forcing a bar or restaurant to accommodate talks, upsetting the normal activities of the space.
From a newcomer's perspective, the daunting aspect of having to present on the first night is alleviated by allowing the new members to integrate and choose whether to participate in the talk-side of the DEF CON group. It should be noted that not all people interested in going to a DEF CON group are currently information security professionals. As networking and general IT professionals are tasked with more security duties than before, and some want to dip their toe in the water to see if a career change would be possible.
Ultimately, we should be able to get something smaller than hacker summer camp, but still valuable out of local DEF CON groups on a regular basis. Leaving the governance of groups ambiguous benefits all DEF CON groups, allowing them autonomy over their region's meetings. We need to do a better job of tracking new members, member retention, and utilizing tools like MeetUp for integrated calendar management and site permanence. We need to seek inclusivity in DEF CON spaces and to get DEF CON groups attached to outside inclusivity focused organizations like WISP or the Women's Society of Cyberjutsu who are already successful in our community. And we need to be honest when things are not working, and to seek advice from the groups and cities that have been successful at developing communities organically.
What framework does your local DEF CON group follow? Tell us if it's working, how is it not working? If you've ever tried to join a group but left and never came back, why? What made you feel the most included? Reach out on Twitter to Secjuice (@secjuice).
Relevant Links:
• Official DEF CON Groups website: https://defcongroups.org/
• Official DEF CON Groups Twitter (@defcongroups): https://twitter.com/defcongroups
• DEF CON Groups Subreddit: https://www.reddit.com/r/DefconGroups/
• Map of DEF CON Groups with MeetUp pages: https://www.meetup.com/topics/defcon/
• 2600 Official List of Meeting Locations / Times: https://www.2600.com/meetings/mtg.html
• Women in Security and Privacy (WISP) Homepage: https://www.wisporg.com/
• Women's Society of Cyberjutsu: https://womenscyberjutsu.org/
• BSides Main Site (includes a map of local BSides events): http://www.securitybsides.com/


