How To Create A Secure Password
Learn how to create a secure password easily and how to protect your data and accounts in this handy guide from security researcher Taharka Beamon.
Passwords are the main gatekeeper between an intruder and your personal and confidential information, so its worth taking the time to explain how to create a secure password, just in case you didn't already know.
With passwords, there are a few general rules: The longer the better, use upper and lower case letters, numbers and symbols or specials characters.
All of these handy tips help ensure your password has complexity and therefore is far less likely to be guessed or hacked.
If you don’t like general rules and want more specifics, The National Institute of Standards and Technology (NIST) created Special Publication 800-63B, an entire document devoted to digital identity guidelines including a large section about passwords.
This article will teach you the important elements of how to create a secure password and protect your data from Hackers.
How Do You Create A Secure Password?
If you have a lot of time on your hands, each time you open a new digital account, you could manually create a new password that contains an upper and lowercase letter, number and symbol that is 8 characters or more.
Then you have to remember the random grouping of characters you threw together in the moment. To make things easier, you can use a passphrase.
Using Passphrases
A passphrase is a word or combination of words that mean somethings to you.
To use a passphrase as a viable password, you could substitute letters in the word(s) with numbers, symbols, random capitalization and extra characters. Passphrases are far easier to remember than a random strings of numbers, letters and symbols.
Password Generators
Both of the previous options are great but they are manual means of password creation. To make things even easier, there are password generators like the one below from LastPass.
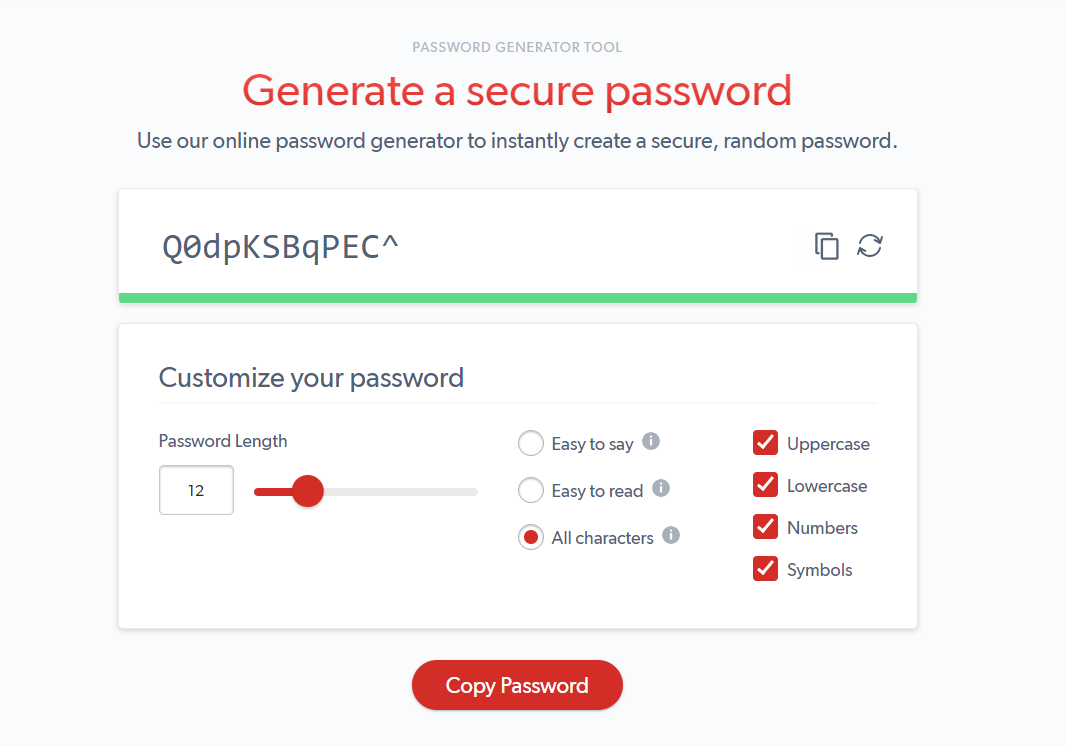
Password generators allow you to input the password criteria such as the type of characters you want included and the desired length and it will create a custom password for you.
How Often Should You Change Your Password?
Now that you have created a unique, secure password for each of your accounts, you never need new password again, right?
Passwords should be changed frequently. Changing your password ensures that if your credentials have been compromised, the previously disclosed login information is no longer valid. Additionally, if someone is trying to guess your password manually or in an automated fashion using software, their attempts will not be able to continue perpetually against the same static password.
Passwords are often mandated to be changed at specified time intervals based on the software’s defined rules or corporate policy.
The Debate
Throughout the years, the recommendation on when to change your password has been amended. Previously, the convention of requiring password changes every 30, 60 or 90 days was accepted as the standard.
In 2017, with the publication of NIST Special Publication 800-63B, the recommendation is now to empower users to change their passwords periodically at their discretion unless there is evidence of a breach which would require more immediate action.
Password Managers
When it comes to creating, storing and managing secure passwords, password managers are the one-stop option.Using a password manager, you can automatically generate new secure, unique passwords based on the criteria of your choosing. Once the password is created, the password is securely stored in an encrypted password vault.
When you need to provide your credentials across the web, you do not need to remember dozens of secure passwords. The password manager can automatically fill in the password field or other form data for you.
Learn more about The Best Password Managers and Why You Should Use One in my last article on Secjuice.
Password Attacks
There are dozens of attacks against passwords that could lead to someone accessing your personal information or impersonating your identity.
Four of the more well-known attacks against passwords are:
• Dictionary Attack: An attack that tries all phrases or words in a dictionary or precompiled list, trying to crack a password or key.
• Brute Force Attack: Attempts to uncover passwords by guessing all combinations of the alphanumeric and other characters allowable.
• Rainbow Table Attack: A rainbow table is a precomputed table used for reversing cryptographic hash functions for the purposes of cracking password hashes.
• Phishing: A social engineering attack that uses email in an attempt to trick unsuspecting recipients into supplying passwords and other information by masquerading as a reputable or known company to the user.
Software Built To Harvest Your Passwords
The task of cracking and stealing passwords has become more effortless over time. Anyone can download software that is built to allow hacking novices to start a password-based attacks with a few clicks.
Notable software titles include John the Ripper, Cain and Abel and Ophcrack.
It is important to note that the aforementioned software, despite the ability to be used for malicious purposes, are free of charge and can downloaded for all of major operating systems or come included in OSes such Kali Linux.
Conclusion
Protecting your identity, accounts and information online starts with creating a secure password. This article explained what makes a secure password, how to create a secure password and the attacks that can cause a password to be compromised. Additionally, we spoke about the tools Hackers use to crack passwords and the relative ease with which anyone could gain access to this type of software and begin password retrieval activities.
Protect yourself and your data online by following the principles of creating secure passwords or use a password manager to help manage the essential tasks of creating, storing and distributing your password with little effort.
Are your accounts safe from Hackers?

