How to Hunt Your Way through Bug Bounties
Getting started in bug bounties can be rough. Learn how to get started on the right path.
Let's get started in hunting them bugs and get a killer bounty. I'm sure you have heard of bug bounties. There are many platforms providing web applications for hackers to hunt for bugs in return for a bounty of size depending on its severity. Bug hunting is entirely different from penetration testing and on a whole different level. This guide touches on the basics of how to get started in the bug bounty trend, but look for an upcoming series I am writing about bug bounties, a methodology, and how to get paid for finding some good bugs. Bug bounties require a mass amount of patience and persistence. You won't become a bug hunter overnight, but this article can get you on the right path to become one. Even when you start looking for bugs, it might take you a while to start finding them in a real-life platform, but there is plenty of help and guidance along the way.
Starting Point
If you have a few infosec friends on Twitter, look at their posts because they always posting things like, "I found this bug and that bug," and "I got this much reward for finding it." If you have ever wondered, "how can I get started in bug bounty?" then keep reading. Just remember, we will learn how to walk before running, but it's well worth the effort! Let's take a look at web applications.
What are Web applications?
Web applications are applications made by developers as a client-server computer program which the client runs in a Web browser or any Web technology that runs over the Internet.
A Web server is what stores and sends the developer's code to the client on-demand to run the web site scripts and files. There are various resources which provide deeper learning; check out the MDN web docs 'What is a web server?'
So now that we know what web applications and servers are, it's essential to know the protocol behind the apps that makes the client-server talk to each other: that would be HTTP (HyperText Transfer Protocol).
It's essential to learn about HTTP as a starting place to understand how messages are sent back and forth to clients and web servers. You understanding HTTP will help you develop that relationship to get started as this is the fundamentals you need to get your head around. Here is a starting point from the MDN wen docs 'An overview of HTTP'
Networking is also another essential topic you need to learn, learning the basics of networking along with the OSI/TCP model to learn how data gets sent from the application layer to the physical layer and vice versa also learning DNS protocols and various other protocols around the network.
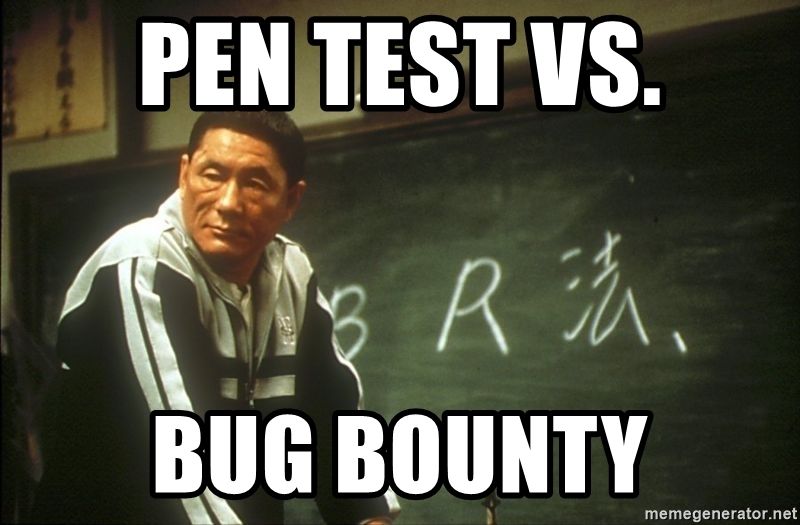
Linux and the command line is essential to learn, learning command-line techniques, and how to get yourself around Linux, there are some great resources out there and some Linux command line cheat sheets to put up as wallpaper as a reference is also very helpful when your learning command lines. Another resource to bookmark is'command line fu' and there are plenty more websites for learning it. Linux is free to use, and distributions like Kali Linux or Parrot OS is a great place to start, download one and run it in a VM to get started.
Basics of code
Many testers make a point that they have found so many bugs but don't know how to write one line of code, yes this can be done, but later down the line, that same tester says he or she is learning the basics of code. There's only so far you can get until you feel like you need to take the plunge into the pool of code. You don't have to be a master writer. You mainly need to learn the basics, understand how to read the code, and understand what it's trying to do. Most of the time, reading and inspecting code is what you do; how can you break something if you don't understand it? Yes, you can run tools and not knowing what you're doing and break something but then how do you fix it? How can you advise the developers on what needs fixing? However, you learn through experience but first is to learn the basics of what's going on behind a website.
My advice would be to learn the core basics of HTML, CSS, Javascript and some PHP, it's not going to be an easy journey in learning Javascript, but learning the core basics and understanding what is going on is important <script>alert(“You have been hacked”)</script> this is a basic one line of code that can be inserted into HTML using the script tags to pop up a box saying “You have been hacked”, we use this to test for XSS, we can send this to the web server using the POST method to store it on the server so every time a user goes on to that website it will load that script each time.
My recommendation is to start with web applications before looking at mobile applications to get an understanding of what's going on and a lot easier to learn but if you want to get into mobile applications then dive straight into there, there is nothing in stopping you from learning that first just about finding your way through all the bad stuff to get to the good stuff.
Web Application Security
First things first is to bookmark this site: Owasp.org
We will be using OWASP as a guideline in web security starting with the OWASP Top Ten 2017 guide, this will give you an understanding of vulnerabilities, risks and awareness that are out in the web application field the OWASP Top Ten dates back to 2010 where you can go back to see other vulnerabilities just because its dated in 2010 doesn't mean you won't find it, when hunting for bug.
OWASP Testing guide 4.0 is next on the list this book is over 200 pages so if you don't like reading then try to watch as many videos on this topic as much as you can but the best way to learn is to read small bits of the testing guide and then put that into a practical hands-on experience which I will show you how to practise and give you plenty of resources to get your hands dirty.
There are various books to help you get started and to cross-reference with anything you find in the field:
- Web hacking 101
- The web application hackers handbook
- Masting Modern Web Penentration Testing
- Breaking into information secuirty by andy gill
If you not into books then there plenty of videos out there I will write a whole resource list at the bottom of this blog.
Tools of the Trade
A great tool out there to use is OWASP Zed Attack Proxy (ZAP). It finds web vulnerabilities in web applications, it is easy to use, and it is free to use. I prefer this over other tools out there, but there is another excellent tool called Burp Suite, which I use religiously. It is simple to use, but the downside is there is a pro version which costs money, but well worth the money. I can't write off either one as they both are fantastic to use, as long as you find one that you prefer rather than choosing your friend's personal preference. There are many tutorials of how to set these up and use them search on YouTube, again I will be writing a list of resources to help you weed out the old stuff out there.
Practise makes perfect
Moreover, lots of practice you will need. Don't worry, I got you covered for all your needs. It's essential to keep yourself updated with the latest vulnerabilities and tools that will make your life easier. This is a long journey and will take some time to understand and get your head around, but patience and persistence will help you. Once you start grasping the concepts, then you will be on your way these resources below will help you.
Online Resources
- Hacker101
- PenTesterLabs
- Bug Bounty Notes
- BugCrowd University
- XXS Game
- OverTheWire
- Hack Me
- HackTheBox
VM Resources
- Vulnhub
- Damn Vulnerable Web Applications (DVWA)
- Metasploitable 3
- OWASP Security Shepherd
- OWASP Juice Shop
Start with the basic online resources that will give you that hands-on experience and once you have worked through the online resources. Then go onto the VM resources, where you download each box and load it into a VM. If you check my blog about VM’s, it will explain how to download and configure the boxes ready for you to test. If you are to go through the OWASP Top Ten, then I recommend reading that with OWASP Juice Shop, as the juice shop has all the OWASP Top Ten vulnerabilities.
Platforms
Once you are confident to start hunting, then check out real-life bug bounty platforms where you can hunt for live bugs in real apps and get paid. An important tip here for you is that it will take you months to find your first bug and when you do submit your first bug it may not be what you think it is. Don't let that discourage you or take away your confidence because if you ask the best hunter out there, they will all have the same story!
There are many more platforms you can use, google to find more but the top two are hackerone and bugcrowd also big platforms like Facebook has there own bug bounty programs search the company with ‘bug bounty’ and will come up with there page.
Read the terms
Before you start testing, please read the disclosure and terms plus keep within the scope, often I see newbies go out of scope, you don't want to start any dramas and a headache, please be responsible for yourself and the actions you take. Give adequate time for the companies to act on any bugs that need fixing and not to post a vulnerability until its fixed publicly.
Once you found a bug, you will get this crazy sensation inside and want to dance around and show off your findings but don't! You will need to start writing up a POC (Proof Of Concept) and show how you did it, write how severe the bug is and what the fix is. If you take a look at HackerOne’s hacktivity which you can see POCs, this will give you an idea in what kind of POC you would need to write. Spend some time on hackerone's hacktivity and read through some of the reports other hunters have written. It will teach you all types of vulnerabilities, and how they did it, that is another learning resource and will keep you up to update with new vulnerabilities.
Shout Outs
There are some great people out in the community and can learn a lot from them add them on twitter subscribe to there channels or blogs as they will keep you up to date with the latest and greats tips and tricks or even vulnerabilities.
- HackerSploit @HackerSploit
- Jason Haddix from bugcrowd @Jhaddix
- STÖK @stokfredrik
- Zseano @zseano
- LiveOverFlow @LiveOverflow
- Web Development Tutorials
- HackersEra @OffensiveHunter
- IPPSEC @ippsec
There are plenty more to follow, but these will get you started on twitter and there youtube or websites, these are all talented people and will learn so much from them, especially HackerSploit and Vikash from HackersEra his training is well worth the money and can easily make your money back from his program.
I am not affiliated from any of these guys; they are just good friends I have made along my journey in bug bounty and have so much love to give back as I have learned so much from them. Feel free to contact them on Twitter or their platform of choice; they are friendly and always giving advice, but, keep in mind, they are very busy with what they do.
I hope this has helped you in your journey into bug bounties. Look out for my series on bug bounty blogs where I go deeper into bug bounties. Assuming that you have done all your homework above, we will be cracking on with the good stuff. For now, take care and all the best.
YouTube Videos
- HOW TO GET STARTED IN BUG BOUNTY (9x PRO TIPS)
- Bug Bounty Hunting - Tools I Use
- LevelUp 0x02 - Bug Bounty Hunter Methodology v3
- Bug Bounty 101 - How To Become A Bug Hunter - Bug Bounty Talks
- The Truth About Recon (Bug Bounty Tips)
- BUGBOUNTY PRO TIPS FOR BEGINNERS: With Nahamsec
- Offensive Approach to Hunt Bugs | Vikash Chaudhary | OffensiveHunter