Squeeze Volume 14 - KidsGuard, VPN backdoors, Bluetooth, MGM & more!
Welcome to Squeeze, a curated selection of interesting infosec articles from the past week that you may have missed.

Welcome to the 14th edition of the Secjuice Squeeze, where we present a selection of last weeks interesting infosec articles curated for your reading enjoyment in case you missed them! This week's volume compiled by the Secjuice team: Bhumish Gajjar, and Mike Peterson.
Iranian hackers have been hacking VPN servers to plant backdoors
According to a report from Israeli cybersecurity firm ClearSky, Iran's government-backed hacking units made a top priority last year to exploit VPN bugs as soon as they became public in order to infiltrate and plant backdoors in companies all over the world. They have targeted companies from the IT, Telecommunication, Oil, and Gas, Aviation, Government, and Security sectors.
ClearSky says that "Iranian APT groups have developed good technical offensive capabilities and can exploit 1-day vulnerabilities in relatively short periods of time."

Unsafe WordPress Plugin Installed on ~200,000 Sites
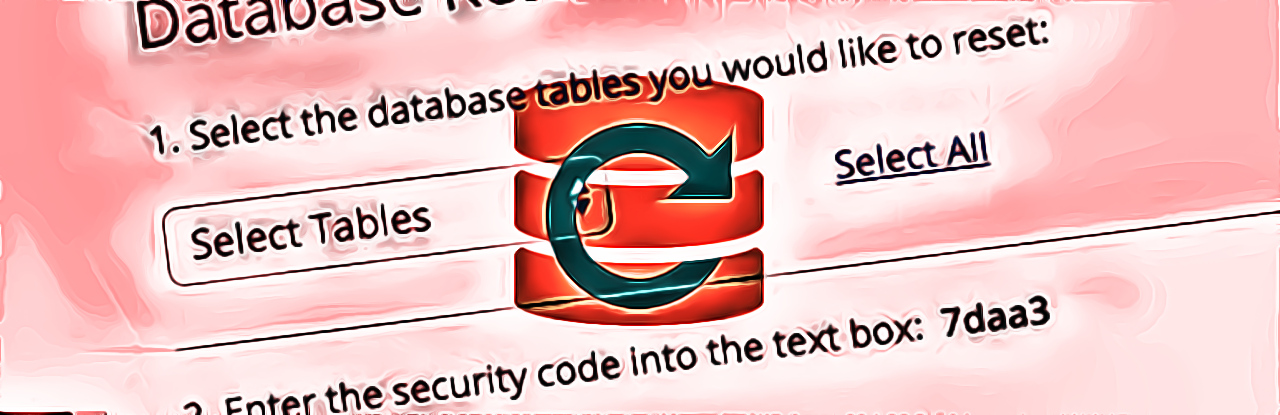
The developers of the ThemeGrill Demo Importer for WordPress have updated the plugin to remove a critical bug that gives admin privileges to unauthenticated users. In the process of getting logged in as an administrator, the attackers also restore the site's entire database to its default state.
Wiping the database of a vulnerable site requires a theme developed by ThemeGrill to be active. Since the plugin is installed, there is a chance that a theme from the developer is active.
A Dozen Vulnerabilities Affect Millions of Bluetooth LE Powered Devices
A team of cybersecurity researchers late last week disclosed the existence of 12 potentially severe security vulnerabilities, collectively named 'SweynTooth,' affecting millions of Bluetooth-enabled wireless smart devices worldwide—and worryingly, a few of which haven't yet been patched.
All SweynTooth flaws basically reside in the way software development kits used by multiple system-on-a-chip (SoC) have implemented Bluetooth Low Energy wireless communication technology—powering at least 480 distinct products from several vendors including Samsung, FitBit and Xiaomi.
Link: https://thehackernews.com/2020/02/hacking-bluetooth-vulnerabilities.html

Mozilla launches a VPN app for Android and Windows
Mozilla, the organization behind the Firefox browser, is bringing its VPN (Virtual Private Network) service to Android and Windows 10 through a dedicated app. You need to pay $4.99 a month because privacy is not a free lunch. In return, Mozilla vows not to log your network traffic or your browsing history.
The VPN uses a new Wireguard protocol, which is supposed to be faster and more secure than other standards such as OpenVPN. Mozilla said with the app, you’ll be able to connect five devices simultaneously and use servers located in more than 30 countries.
Link: https://thenextweb.com/privacy/2020/02/19/mozilla-launches-a-vpn-app-for-android-and-windows/

DHS says ransomware hit US gas pipeline operator
A ransomware attack has impacted the operations of a US-based natural gas compression facility, according to a security advisory from the US government.
The incident took place after "a cyber threat actor used a spearphishing link to obtain initial access to the organization's information technology (IT) network before pivoting to its operational (OT) network." After gaining access to the OT network, the attacker then deployed commodity ransomware that encrypted the company's data on both the IT and OT networks at the same time, for maximum damage, before requesting a ransom payment.
Link: https://www.zdnet.com/article/dhs-says-ransomware-hit-us-gas-pipeline-operator/

Feds charge California man with politically-motivated DDoS attack on candidate website
Last week, the FBI arrested a Santa Monica man on charges of carrying out a distributed denial-of-service attack on a California congressional candidate's website back in 2018. During the midterm elections in April and May of that year, the man carried out four separate DDoS attacks that took down the candidate's website for a total of 21 hours.
The Santa Monica man, identified by the DoJ as 32-year-old Arthur Jan Dam, was found by The Intercept to be connected to the Katie Hill campaign. (The cyberattacks targeted Hill's primary opponent.) While Hill won that race but eventually resigned amid controversy, the attacks go to prove that not all cyber threats come from foreign actors.
Link: https://theintercept.com/2020/02/21/fbi-arrests-hacker-linked-to-katie-hill-campaign/

MGM Resorts admits to 2019 data breach that leaked info on nearly 10 million former guests
Hospitality and resort company MGM admitted that someone accessed one of their servers that contained information on more than 10 million guests, including some high-profile customers. According to a joint report by Under The Breach and ZDNet, that information included full names, home addresses, phone numbers, emails, and dates of birth. That data ended up posted on various hacking forums.
MGM insists that no extremely sensitive data, like financial information or social security numbers, were leaked. But data privacy advocate Ray Walsh at ProPrivacy indicated that about 1,300 users did have information from identity documents and passports compromised in the breach.

Stalkerware app 'KidsGuard' was leaking all of the data it collected to the internet
Spyware apps intended originally for parents monitoring their kids are banned from the Google Play Store and iOS App Store. That's because these apps can collect data on pretty much everything a smartphone user does, including real-time location, call history, app activities, and photos. And this morning, TechCrunch discovered one reason why these apps are banned.
A spyware or stalkerware app known as KidsGuard was allegedly secretly installed on thousands of smartphones without their user's knowledge. Worse still, all of that sensitive data was being stored in a public Alibaba bucket that wasn't secured by a passcode. Just one more reason to give these apps a wide berth.
Link: https://techcrunch.com/2020/02/20/kidsguard-spyware-app-phones/







