Secjuice Squeeze Volume 45
Welcome to the Secjuice Squeeze, a curated selection of security articles and infosec news that you may have missed.
Welcome to the Secjuice Squeeze, a curated selection of interesting security articles and infosec news that you may have missed, lovingly curated for you every week. This week's volume was curated by Secjuice writers Hartoyo Wahyu, Prasanna, Sinwindie, Muhammad Luqman, and Thunder-Son.
Articles
Windows 10, iOS, Chrome, Firefox and Others Hacked at Tianfu Cup Competition
Multiple software products from Adobe, Apple, Google, Microsoft, Mozilla, and Samsung hacked at Tianfu Cup 2020.
Source & Link: thehackernews.com
Curator: Hartoyo Wahyu
Npm Package Caught Stealing Discord & Browser Files
Malicious code was found hidden inside a JavaScript library named Discord.dll.
Source & Link: zdnet.com
Curator: Prasanna
Former Microsoft Engineer Sentenced To Nine Years
The former software engineer used other employees' accounts to steal digital gift cards among other crimes.
Source & Link: zdnet.com
Curator: Prasanna
Millions of Hotel Guests Caught Up in Mass Data Leak
A cloud misconfiguration affecting users of a popular reservation platform threatens travelers with identity theft, scams, credit-card fraud and vacation-stealing.
Source & Link: threatpost.com
Chrome Block JavaScript Redirects On Web Page URL Clicks
Google Chrome is getting a new feature that increases security when clicking on web page links that open URLs in a new window or tab.
Source & Link: chromium.org, bleepingcomputer.com
Your Cop-Friendly Spy Device Could Burst Into Flames
After receiving 85 reports of doorbells catching fire, Ring has issued a recall of some second-generation Ring doorbells (the one with the blue ring) for igniting and causing "minor property damage."
Source & Link: gizmodo.com
Curator: Sinwindie
Binance Grants $200,000 to Investigators for Identifying Exchange Hackers
Binance announced today that it has awarded $200,000 to investigators for providing information about attackers and for the details about the attack.
Source & Link: financemagnates.com
Curator: Sinwindie
Microsoft Beg Users To Stop Using SMS based MFA
Microsoft recommends using app-based authenticators and security keys instead.
Source & Link: zdnet.com
Microsoft Teams Users Under Attack in 'FakeUpdates' Malware Campaign
Microsoft warns that cybercriminals are using Cobalt Strike to infect entire networks beyond the infection point, according to a report.
Source & Link: threatpost.com
Curator: Muhammad Luqman
2 New Chrome 0-Day Vulnerabilities Under Active Attacks
Recently, Google has released two new patches for two new actively exploited vulnerabilities in Google Chrome. read more here.
Source & Link: cybersecuritynews.com
Curator: Muhammad Luqman
Facebook sues Turkish software developer who ran 20+ Instagram clone sites
Facebook says the Turkish developer operated Instagram clone sites like jolygram.com, imggram.com, imggram.net, finalgram.com, pikdo.net, and ingram.ws.
Source & Link: zdnet.com
Curator: Prasanna
How the U.S. Military Buys Location Data from Ordinary Apps
A Muslim prayer app with over 98 million downloads is one of the apps connected to a wide-ranging supply chain that sends ordinary people's personal data to brokers, contractors, and the military.
Source & Link: zdnet.com
Curator: Thunder-Son
Facebook Messenger Bug Lets Hackers Listen to You Before You Pick Up the Call
A Bug in Facebook Messenger App for Android Could've Let Hackers Listen to the Person You Are Calling Before Even They Pick Up.
Source & Link: thehackernews.com
Curator: Thunder-Son
Massive, China-state-funded hack hits companies around the world, report says
Attacks are linked to Cicada, a group believed to be funded by the Chinese state.
Source & Link: arstechnica.com
Curator: Sinwindie
DeFi Protocol Pickle Finance Hacked For $20 Million
The coffers of Pickle Finance, a decentralized finance (DeFi) protocol, were drained today of $20 million in what appears to be a hack.
Source & Link: decrypt.co
Curator: Sinwindie
How an Online Attack ‘Brought Twitter to Its Knees’
A teenager from Florida is accused of breaching one of the most high-profile internet platforms in the world. Watch how Twitter was hacked in a new Times documentary airing tonight on FX at 10 p.m. and streaming on Hulu.
Source & Link: nytimes.com
Curator: Sinwindie
Cryptocurrency exchange Liquid confirms hack
An investigation is underway to see if hackers accessed documents that users submitted to verify their information with the exchange.
Source & Link: techcrunch.com
Curator: Sinwindie
Hackaday Podcast 094: Fake Sun, Hacked Super Mario, Minimum Viable Smart Glasses, And 3D Printers Can’t Do That
Hackaday editors Elliot Williams and Mike Szczys traverse the hackerscape looking for the best the internet had to offer last week.
Source & Link: hackaday.com
Curator: Sinwindie
Nintendo sues more hack sellers, ‘a worsening international problem’
Another lawsuit filed in Seattle court.
Source & Link: polygon.com
Curator: Sinwindie
IBM Works With Cisco to Exorcise Ghosts From Webex Meetings
IBM found openings in Webex Meetings that could let 'ghosts' listen in. Now patched, the vulnerabilities show the importance of securing remote work tools.
Source & Link: securityintelligence.com
Curator: Sinwindie
Hackers Dupe GoDaddy Into Helping Them Take Down Cryptocurrency Sites
Roughly one year after a data breach at GoDaddy compromised 28,000 customer accounts, the world’s largest internet domain registrar is once again at the center of a security scandal. Hackers brought down several cryptocurrency services using GoDaddy domains in recent weeks, and apparently the company’s own staff unwittingly helped in these attacks.
Source & Link: gizmodo.com
Curator: Sinwindie
Upcoming Events, Webcasts, Conferences, etc.
BIG List of Virtual Cybersecurity Conferences
Source & Link: https://github.com/santosomar/virtualseccons
Curator: Guise Bule

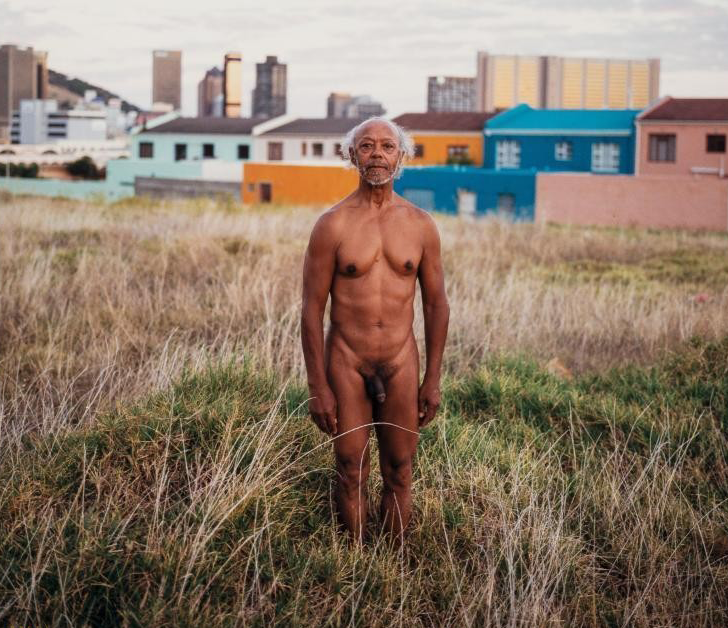
About The Artwork Used In This Article
You may have noticed that we often like to break the norm where an article's image must be relevant to the article's subject, we find it liberating. In this issue, we push the boundaries a little more with some thought-provoking imagery and by showcasing a specific artist. We like to showcase the work of illustrators, designers, and artists when choosing our images, but have never really showcased the work of a photographer before. We thought it was time to change that. True to our form, we chose a subject matter completely unrelated to infosec.
Welcome to the wonderful world of Spencer Tunick, an artist who has been documenting the live nude figure in public since 1992. Tunick has been arrested five times while attempting to work outdoors, the charges were later dropped but the threat of arrest haunted him constantly.
Determined to create his artwork on the streets, he filed a civil rights lawsuit to protect him and his participants from arrest. In May 2000, the Second US district court sided with Tunick, recognizing that his work was protected by the First Amendment of the US Constitution.
In response to New York city's final appeal to the US Supreme Court, Justice Ruth Bader Ginsburg ruled in favor of Tunick by remanding the case back down, allowing the lower court decision to stand and the artist to freely organize his work on the streets of New York City.
Learn more about Spencer Tunick and his art using the links below: