TryHackMe Ohsint Writeup
A technical write up of the TryHackMe Ohsint room from information security researcher Muhammad Luqman.

Ever wondered how the data you share on the internet could be used to extract sensitive information about you? As a proof of concept, we are going to solve Room Ohsint available on the TryHackMe Platform. The room consists of 7 tasks altogether which we will go through one by one. So let's dive in !!!
P.S: I have made some of the task answers unreadable so you folks don't just copy-paste to get the right answers, I encourage you to try and solve them by yourself.
Information Gathering
Before we get started with task 1, we are supposed to download a picture, which you quickly realize is an iconic picture of Windows XP Desktop.

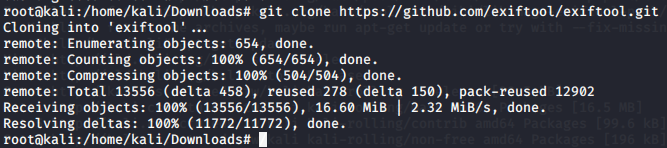
After we download this, we need to get more information about this image. The tool we are going to use to extract the metadata of the image is ExifTool. We need to download and install it first, I am going to install it using Github.
Once installed we are going to run it and we get the following information about the image.

Analyzing the above information we come to know that owner of this image is OWoodflint. Now we search this user on google in order to extract more information. We find the following links associated with the author. We need to explore it one by one. If we look at the task we need to find the avatar that the author is using.

Task 1
Let us first explore the blog. Upon exploring the blog we don't find anything useful there yet, so we move on to the user's Twitter account and here we find the answer to our first question.

Task 2
Next, we need to find the location of the user. So exploring his social media account i.e. twitter we come to know that he has shared the BSSID which actually depicts the MAC address of the WAP (Wireless Access point). So how can we use this information for our use?? We will use wigle.net which is used to gather information on all the hotspots or WAP around you. We use the BSSID to gather more information about the user. Remember to make an account on wiggle.net for accurate results. Now we get the answer to our task 2.

Task 3
We know the location of the user, exploring a little further we also come to know the SSID he is associated with reference to the BSSID he shared on his Twitter account. This gives us the answer to task 3.
Task 4 & 5
Next, we need to find the user email address, let us check out the Github link associated with the user. We get the email of the user from the Github link as shown below. That answers our task 4 and 5 questions.

Task 6
Now we need to visit his blog again which answers our question to task 6 as shown below.

Task 7
In this task, we need to find out the user's password. So we do a little research, we saw the user social profile and the Github link which did not give us any information regarding users' passwords. So we go the blogpost again, after spending some time on the blog site we inspect the source code and found something which had a pattern that depicted a password. Like seriously OWoodFlint you need to find a better place to store your password. This finishes our task 7 and the room is completed

Conclusion
After going through the above tasks, we conclude that even a small piece of information could lead to uncovering many details about a person and his whereabouts over the internet. A helpful reminder that we should be careful with what we share on the internet publicly.
About Me
I am a cybersecurity enthusiast pursuing my Master’s in Information Security and trying to get into a full-time cybersecurity career.


